The Carnabank case
In the world of cybercrime, 2013 marked a new era. It saw the birth of the Carbanak group (also known as Anunak or FIN7), which, instead of robbing individual users, targeted the very heart of the system: banking infrastructure. In just a few years, hackers siphoned over a billion dollars from more than 100 financial institutions across 30 countries.
The "Patient Hunter" Strategy
Unlike typical cybercriminals, Carbanak did not operate using a "hit and run" method. According to the Kaspersky Lab report, "The Great Bank Robbery," the group mastered the art of patience to perfection.
Infiltration via "Poisoned" Correspondence
Internal Espionage 
- Recorded the work of cashiers and system administrators.
- Learned specific jargon and transfer approval procedures.
- Analyzed the bank's working hours and settlement cycles.
The Four Pillars of Theft
Once the hackers knew the system better than the IT staff, they launched the cash-out operation. Reports from Group-IB and Europol highlight several primary methods:
1. SWIFT System Manipulation (International Transfers)
This was the most lucrative method, allowing the group to steal millions of dollars in a single transaction.
· Mechanism: After gaining access to the workstations of employees responsible for the SWIFT network, hackers transferred funds from the bank's internal accounts to their own foreign accounts.
· Details: They utilized their deep knowledge of banking procedures (gathered during months of internal espionage) to ensure transfers appeared authorized and aligned with the bank’s official schedule.
2. ATM "Jackpotting" (Remote Cash Dispensing)
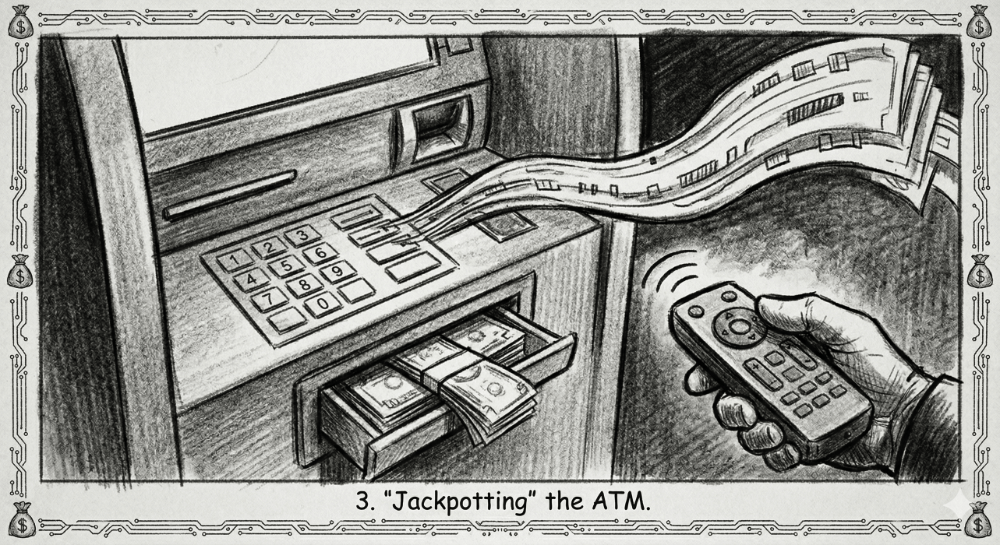
· Mechanism: Hackers took control of the servers managing the ATM network and sent a remote command to a specific machine to dispense all its cash cassettes at a predetermined time.
· Details: Simultaneously, a "money mule" (often recruited by local organized crime) would stand by the ATM to collect the cash as it automatically slid out of the tray. This was possible only due to the total compromise of the bank's internal network.
3. E-Payment System Infiltration
The hackers targeted systems processing online transfers and prepaid cards.
· Mechanism: Rather than attacking individual customer accounts, the hackers breached the bank’s accounting systems directly and moved funds to accounts in China or the USA.
· Details: They frequently used "intermediary" systems to mask their tracks—money was first moved to e-wallets or prepaid cards, which were later emptied by the group's associates.
4. Database Manipulation and "Account Inflation"
This was the most subtle method, exploiting vulnerabilities in accounting systems.
· Mechanism: Hackers gained access to accounting databases and artificially inflated the balances of selected accounts.
· Example: If a customer had $1,000 in their account, the hackers would change that figure to $10,000. They would then transfer the "surplus" $9,000 to their own account. On the surface, everything appeared correct: the customer still saw their original $1,000 and had no reason to complain, while the bank lost the "excess" funds that hadn't actually existed before the database manipulation.
The Fall of the Leader and an International Chase
For years, the group seemed untouchable due to its decentralized structure. The breakthrough occurred in 2016 in Taiwan, where a mistake by novice accomplices at an ATM allowed local police to secure CCTV footage and make the first arrests.
The final blow was dealt by the Spanish police in cooperation with Europol and the FBI in 2018. The alleged leader of the group, a Ukrainian citizen known as Dennis K., was arrested in Alicante. During the search, assets worth millions of euros were seized, including wallets containing 15,000 Bitcoins. The investigation revealed that the hackers collaborated with Russian and Moldovan mafia organizations, which provided the infrastructure for money laundering.
Legacy: From Carbanak to FIN7
Although the leaders of the original group were convicted, the Carbanak brand evolved. In 2024 reports, experts from Silent Push indicate that the structure has transformed into the group known as FIN7.
Latest Discoveries (2024–2026): Investigators have detected over 4,000 domains linked to the new FIN7 infrastructure. The group has shifted from direct bank heists to "Ransomware-as-a-Service" attacks and data theft from POS systems in hotel and restaurant chains.
Technical Summary:
Primary Malware
Carbanak, Cobalt Strike, Anunak
Number of Victims
Over 100 financial institutions
Estimated Losses
~$1.2 billion USD
Status
Active under the FIN7 / Cobalt Spider banner
The Carbanak case changed the way banks perceive security. It demonstrated that the greatest threat is not a bug in the code, but social engineering and human unawareness. Today, the standard in banking is to monitor not only external attacks but, above all, unusual behavior within one's own network—a direct lesson learned from the actions of this highly intelligent criminal group.
Resources:
https://media.kasperskycontenthub.com/wp-content/uploads/sites/43/2018/03/08064518/Carbanak_APT_eng.pdf
https://sekurak.pl/carbanak-malware-ktory-napada-na-banki/
https://www.group-ib.com/resources/threat-intelligence-reports/anunak-report/
https://www.europol.europa.eu/media-press/newsroom/news/mastermind-behind-eur-1-billion-cyber-bank-robbery-arrested-in-spain
https://www.justice.gov/opa/pr/high-level-organizer-fin7-hacking-group-sentenced-five-years-prison
https://www.silentpush.com/blog/fin7/
https://www.nytimes.com/2015/02/15/world/bank-hackers-steal-millions-via-malware.html