Finding Factories: Using SHODAN To Identify SCADA Devices
Shodan is an extremely useful tool once you’ve taken the time to learn it.
We strive to provide informative articles; however, it is important for users to ensure their research is both ethical and responsible. Additionally, it is your responsibility to ensure you’re compliant with all applicable laws and regulations for your region. The information provided in this article is intended for educational purposes only.
In this previous article, we took a look at the role that SCADA (Supervisory Control and Data Acquisition) systems play in our modern world, and looked at why the radio spectrum plays a key role in transferring data and telemetry over long distances.
While this article touched briefly on the usage of Shodan for identifying and enumerating systems of interest, to make the most of a tool, you’ll need to learn how to use it, and that’s exactly what we’ll be doing today. Shodan does have subscription tiers, but free tier users can still register and follow along. Let’s go!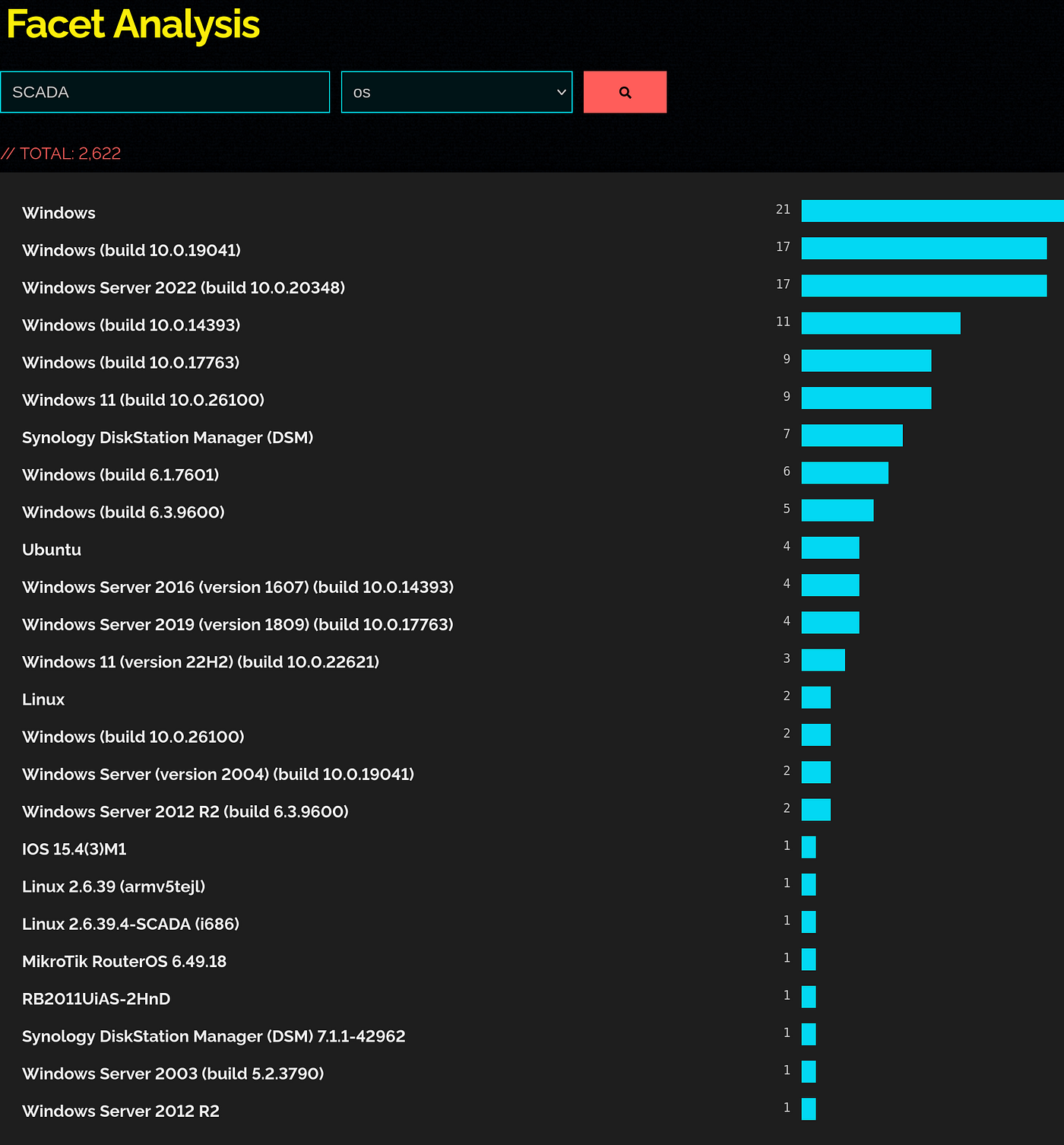
What Is SCADA
Acting as the brains behind many industrial operations, SCADA units control processes, collect data, and in many instances, transfer this data to another part of the operation.
Working in tandem with the PLC (Programmable Logic Controller) or RTU (Remote Terminal Units), elaborate systems can be built, allowing our modern industrial world to work in the way that we’ve become accustomed.
While this is a pretty simple summary, it might surprise you to learn just how deep the SCADA pool gets. Nearly every industrial process, from power generation and water distribution, through to sewage and waste management, is assisted by a SCADA system in some way.
From a cybersecurity perspective, this often leaves SCADA systems in somewhat of a bind. Not only are many of these systems often running on older, less secure technology, but they also often lack encryption and can use wireless links to transmit data and telemetry over long distances.
This, paired with their use in critical infrastructure, means that from a security perspective, there is often plenty to explore.
Asset Identification
To get an understanding of some of these systems, we’ll need to take a look at them, and to do this, we will be using one of the internet’s coolest tools, shodan.io
Useful thanks to its utility, Shodan crawls the internet, capturing banners, system metadata and running services that can be used to identify systems of interest. With a web-based GUI being the choice for many users, power users can opt to use the Shodan API to write their own tools, or use pre-existing tools to automate processes or look for specific conditions.
With good levels of overall support, it really is worth taking the time to read the documents and to familiarise yourself with them. Within these documents, you’ll find lots of useful information that will help you get comfortable with using the platform.
One thing that is particularly nice about the platform is the Filter Cheat Sheet it provides. Here, you’ll find default search filters that you can apply. With the ability to search by ports, services, cities and products, it provides targeted search options that can be easily extracted for further enumeration.
This is going to be useful for a lot of users, but data analysts might be more interested in the “firehose” that can be applied to some accounts. This allows you to access a steady stream of data as it goes live on the platform and is particularly useful for monitoring trends or incidents in real-time.
Today, however, we’re here to search, so let’s look at some of the manual filters that we might be able to apply that will help us find our SCADA devices among the rest of the noise.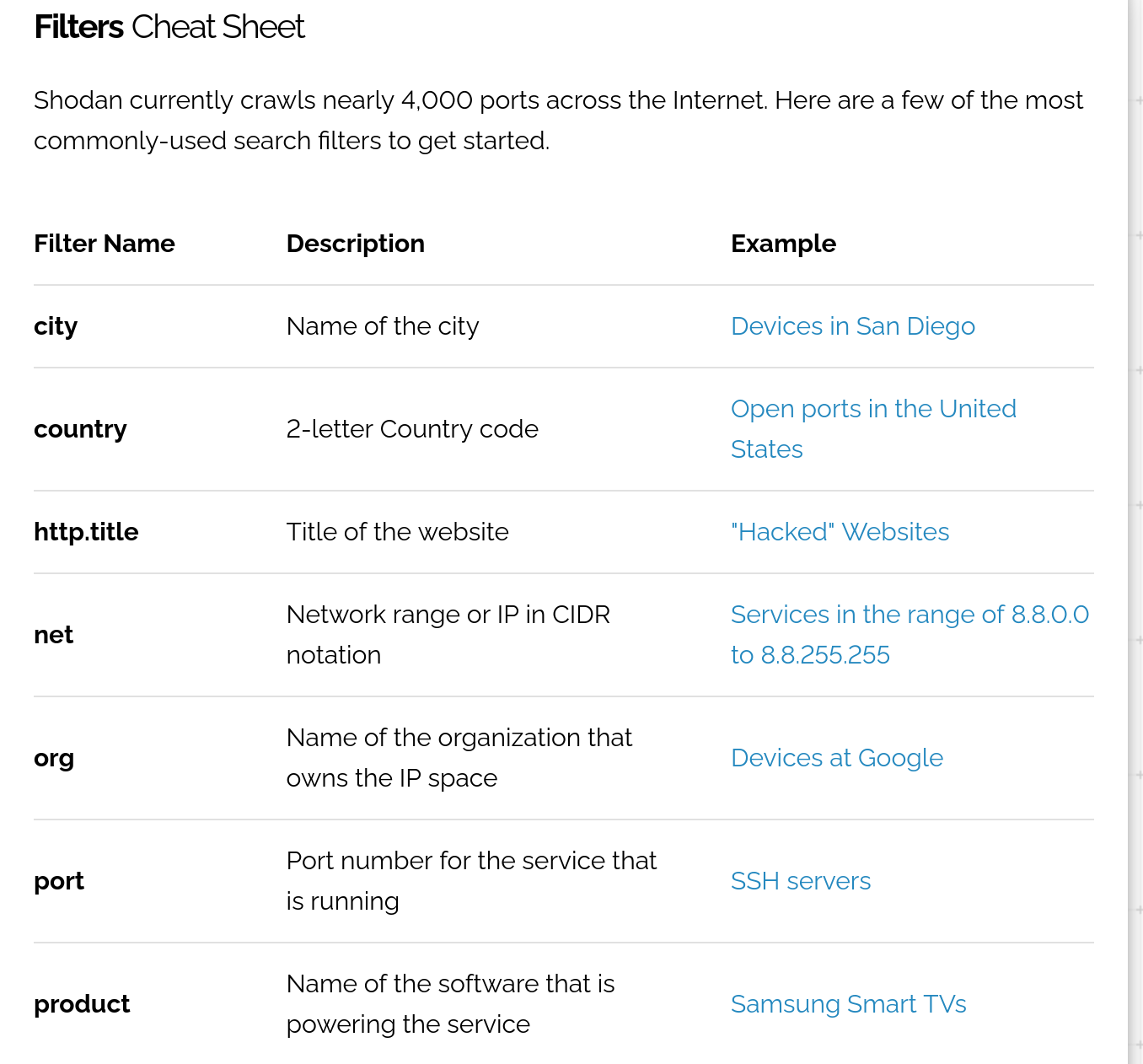
OSINT Go Brrr
We can use known information on Ports and Services to start with. We can also apply some general tags that will help us start to narrow things down a little further. You’ll want to explore this in detail, so for the best results, register your own account and do some digging. To get started, though, you can apply these to generalised systems.
SCADA ICS industrial control PLC RTU HMI
Or, you can use basic combinations to enrich the search results and go a little deeper.
modbus SCADA PLC modbus HMI SCADA S7 Siemens "Modbus TCP" "Modbus RTU" PLC "industrial control"
Let’s face it, no one is here for the basic stuff, and as a tool, we also want to apply it to situations where enumeration can help our situational awareness, not hinder.
Automatic Number Plate Recognition (ANPR) Systems have been in the news a lot lately.
Maybe we could get some interesting search results by applying that with a country-based tag.
anpr country:"US"
For many countries, the war in Iran has messed with the concept of fuel security. Many people are questioning the ability of their governments to maintain the continuity of energy sources. Rather than trust the media, perhaps we can look for some data of our own?
in-tank inventory country "xx"
That was a good one. With more than 5,500 systems online with that single tag, the top ranking reports some interesting information.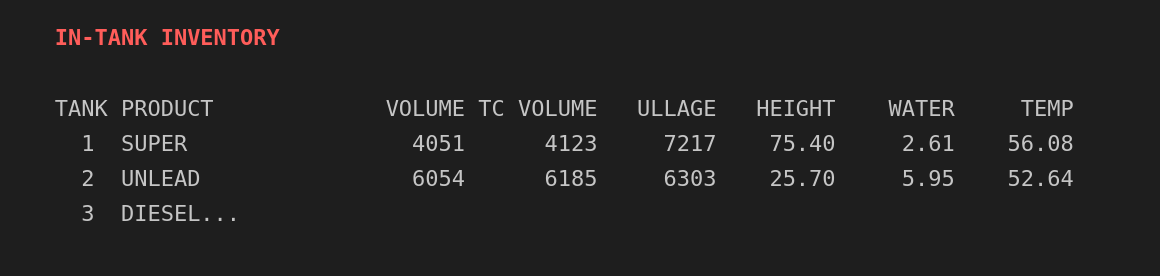
Perhaps we should try another one and see if anyone likes to live dangerously.
no password
More than half a million results on this one. Clearly, some people do like to live dangerously.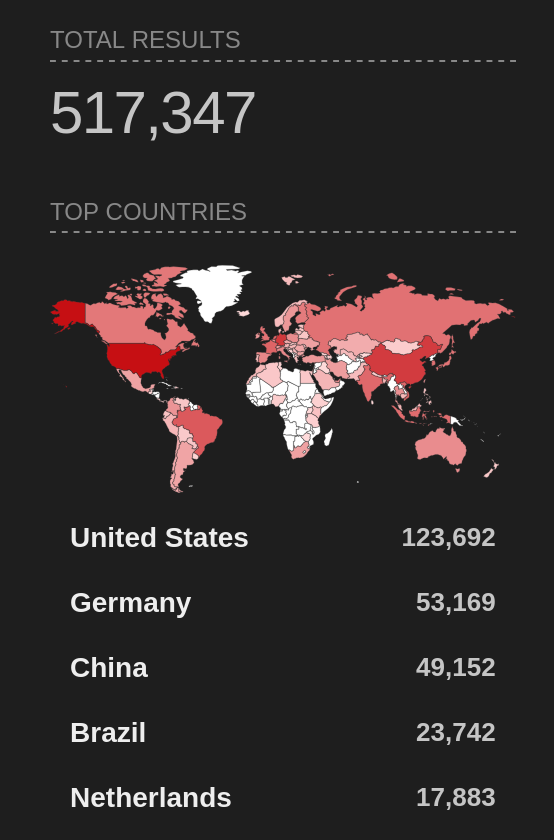
Note: Remember that while searching for devices you don’t own is generally not a crime, accessing devices you don’t own is. So, don’t do that, even if there is no password.
A final search for the simple tag ISM gives us just short of a thousand results, which we can start to use to look harder at devices that emit in the ISM part of the radio spectrum.
It’s worth mentioning that these are just some of the tags you are able to search with. Apply tags that help identify devices within your own field of interest to really get an idea of how things work.
You can also use the “Category” feature that Shodan provides to search by systems via category, giving you more pre-constructed search options that many will find helpful.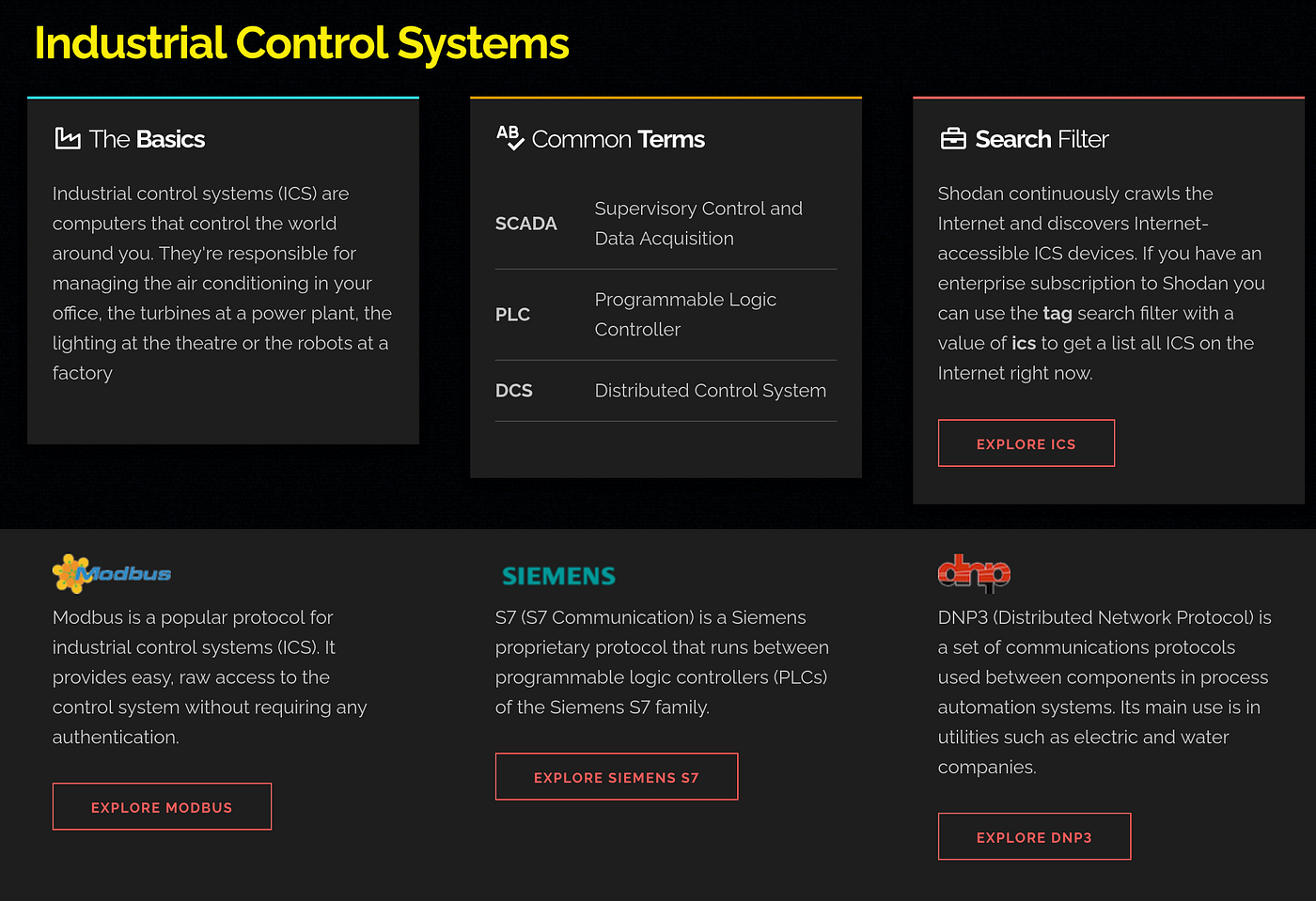
Opinion
In an age of big data, applying accurate search and search methodologies is where many people get stuck. And, while AI can help solve some of these issues, one thing it can’t do is replace good investigative methodology, real-time reasoning and logic at the human level.
Like it or not, big data is here, and the proliferation of Social Media means that in times of crisis, many will find it difficult to leverage accurate, real-time news outside of traditional media sources.
Let’s be clear about one thing. Open Source Intelligence gathering and dissemination is vulnerable to the same strategies as traditional computing. Namely, that bad or unverified data on the input is going to give terrible data on the output.
One thing that we can do with this type of intelligence, though, is apply our own “Big Data” strategies to our workflows to help enhance our access to these techniques. Over the years, breach data has been just one of the sources that has grown significantly as a result of this.
On the offensive side of cybersecurity, there’s a lot of talk regarding enumeration and eventual lateral movement within a network. For data analysts, we can apply our versions of this methodology.
Enumeration comes from analysing data, verifying sources and understanding the situation in greater detail. While the lateral movement comes from knowing where and when to find and use data sources to help give us the most accurate information possible.
Using Shodan today provides a great example of this. While it gives us plenty of data, we still need to cross-check it. Some banners may be old and out of date, while some systems that look like one thing could be honeypots that are another thing entirely. Yes, Shodan can aggregate it for us, but that is only part of the process.
Ultimately, knowing where to look, what to look for and how to verify the authenticity of something is one of the core reasons that investigators exist. Even at the hobbyist level, taking the time to properly develop these skills will pay off in the long run.
Investigator515 explores the RF spectrum, cybersecurity, and the hidden tech behind modern espionage.
Follow for new content weekly
Bluesky • X • Substack
You might also like,
- OSINT Investigators Guide to Self Care & Resilience
- Spies In The Mud: The RF-111 Aardvark
- What The Tech?! Space Shuttles