Bluetooth Security: What Your Devices Are Really Broadcasting
A Counter Surveillance Perspective on Bluetooth Vulnerabilities, Tracking, and Personal Audits
As we’ve worked through some of the wireless fundamentals, we’ve explored the license-free ISM bands and taken a look at some of the vulnerabilities and technical specifications that are relevant to Wi-Fi networks.
While we’ve explored some Bluetooth Exploits in earlier articles, it’s natural that we’d explore the protocol in depth to figure out information on the modulation schemas, explore vulnerabilities and look at tools and software that are available for wireless researchers to use.
We’ll also take a look at how modern Bluetooth works and consider how we might look at carrying out security audits on Bluetooth devices that we own.
There’s a lot to cover today, so let’s get started!
Bluetooth Basics
Modern Bluetooth would change the way we interact with peripheral devices. Allowing us to start the transition to a wire-free world, Bluetooth would help us to create modern headphones, give us the ability to use smart devices and provide a reliable and (mostly) error-free way for IOT devices to communicate information within a local area.
Because it’s become so prolific, standards exist that allow for this reliable method of communication to occur. These standards cover the modulation scheme, power output of devices and channels for the license-free 2.4 GHz band that Bluetooth devices typically operate in.
This standardisation is partly what makes Bluetooth such a reliable communication method. The frequency-hopping, spread-spectrum modulation allows for multiple devices to operate within a vicinity, while the 1MHz or 2MHz spacing of the channels allows for high-speed data transfer with limited packet loss.
Most modern, two-way Bluetooth systems work on a Master/Slave architecture that allows for the usage of different time slots by both master and slave. The master clock ticks with a period of 312.5 μs, two clock ticks then make up a slot of 625 μs, and two slots make up a slot pair of 1250 μs. Real packet sizing may be 1, 3, or 5 slots long, but in all cases, the master’s transmission begins in even slots and the slave’s in odd slots.
We can analyse captured Bluetooth transmissions in detail using some of the wireless tools that we will look at later in the article.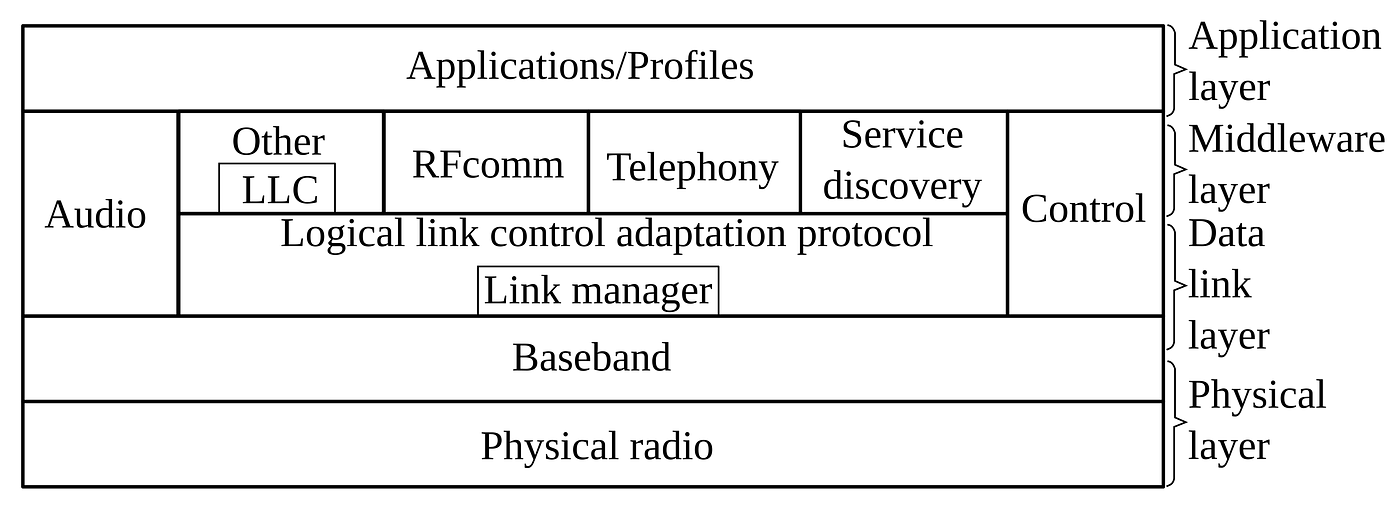
What Is Broadcast?
Like most software, Bluetooth has evolved with time. While we’d start with the OG Bluetooth 1.0, the introduction of more modern standards to cover standard Bluetooth and Bluetooth Low Energy means that now, we are operating at the Bluetooth 6.2 standard as of November 2025.
While looking at the technical stack in the above image is pretty interesting, it’s much more interesting to look at the type of data that modern Bluetooth devices will often emit. This can change according to the device and standards in use, which means that plenty of Bluetooth hardware in the wild has dated standards applied.
This means that security research can be pretty fun, with tools like btscanner and btmon being able to collect some very interesting data.
Typically, this varies according to the device type, but to get an idea of how vast this can be, it’s worth looking at what systems use Bluetooth. Putting aside the obvious car kits and headphones, there are also use cases for:
- Medical devices like Pacemakers and other wearables like fitness trackers communicate health information and metadata.
- Vehicle communications, including infotainment modules, tyre pressure sensor data and battery management system information.
- Industry and manufacturing that includes asset tracking and condition monitoring for things like HVAC systems, which includes telemetry data.
- Home Automation, including smart devices used for automation, air quality telemetry, and device detection that can be used to trigger location-based automations.
It’s worth remembering that some devices will operate in a “non-discoverable” mode. While this doesn’t limit detection entirely, some devices will reduce the amount of information within the packet and operate at a reduced beacon rate in an attempt to enhance overall privacy.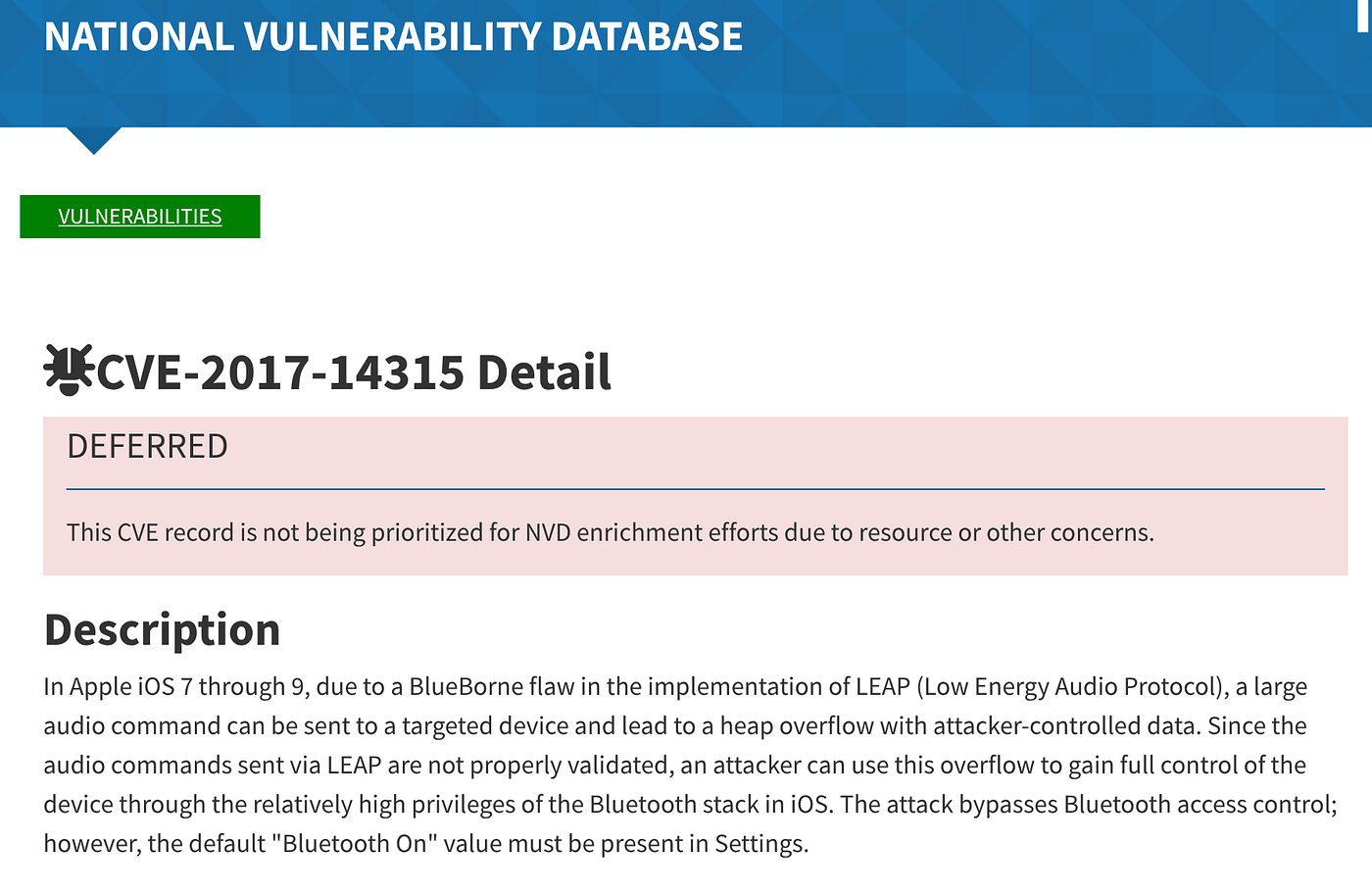
Exploits and Vulnerabilities
Like most RF protocols, as usage has expanded, so has the number of discovered vulnerabilities and attack vectors. Bluetooth is reasonably secure, meaning some attacks are rarely seen in the wild, and patches are often quick to be applied.
However, this isn’t always the case, as some attack vectors use legacy hardware that is slow to be patched or, in the worst case, never patched at all. So this can provide good learning experiences when explored legally within your home test lab.
BLE Spam: Patched on all but the oldest of devices, BLE spam was a denial-of-service attack that flooded devices within an area with connection requests. On some devices, the attack would completely overwhelm the system, leading to a device crash.
Blueborne: A suite of eight flaws (including CVE-2017–0781 and CVE-2017–0785) enabling remote code execution, data theft, and MitM without pairing or user interaction. Attackers exploited stack overflows and information leaks to control devices, affecting Android, Windows, and Linux systems.
BLUFFS: Known as CVE-2023–24023, BLUFFS was a combination of six separate architectural attacks. Designed to force weak session keys, enabling MitM and impersonation, BLUFFS would allow for the extraction of data under some conditions. Affects Bluetooth 4.2–5.4, allowing possible decryption of past/future sessions on large numbers of devices.
Spoofing: Like most RF modes, in some circumstances, Bluetooth spoofing can also be used as an attack vector. This can include spoofing of the device’s MAC information or the use of specific CVEs to exploit known flaws within the hardware or architecture.
Jamming: If you can’t break into the hardware, then some might elect to simply ensure that it can’t be heard. The FHSS mode provides good jamming resistance, however, some threat actors are still capable of causing interference by using these methods. Later variants of Bluetooth (5.0 onwards) would add improved channel selection and better encryption to help offset this.
These are just some of the known attack vectors that exist within the ecosystem. A good look at the National Vulnerability Database will reveal plenty more, so it’s worth taking some time to look through it to learn more about how some of these different vectors were discovered and what the severity ratings are.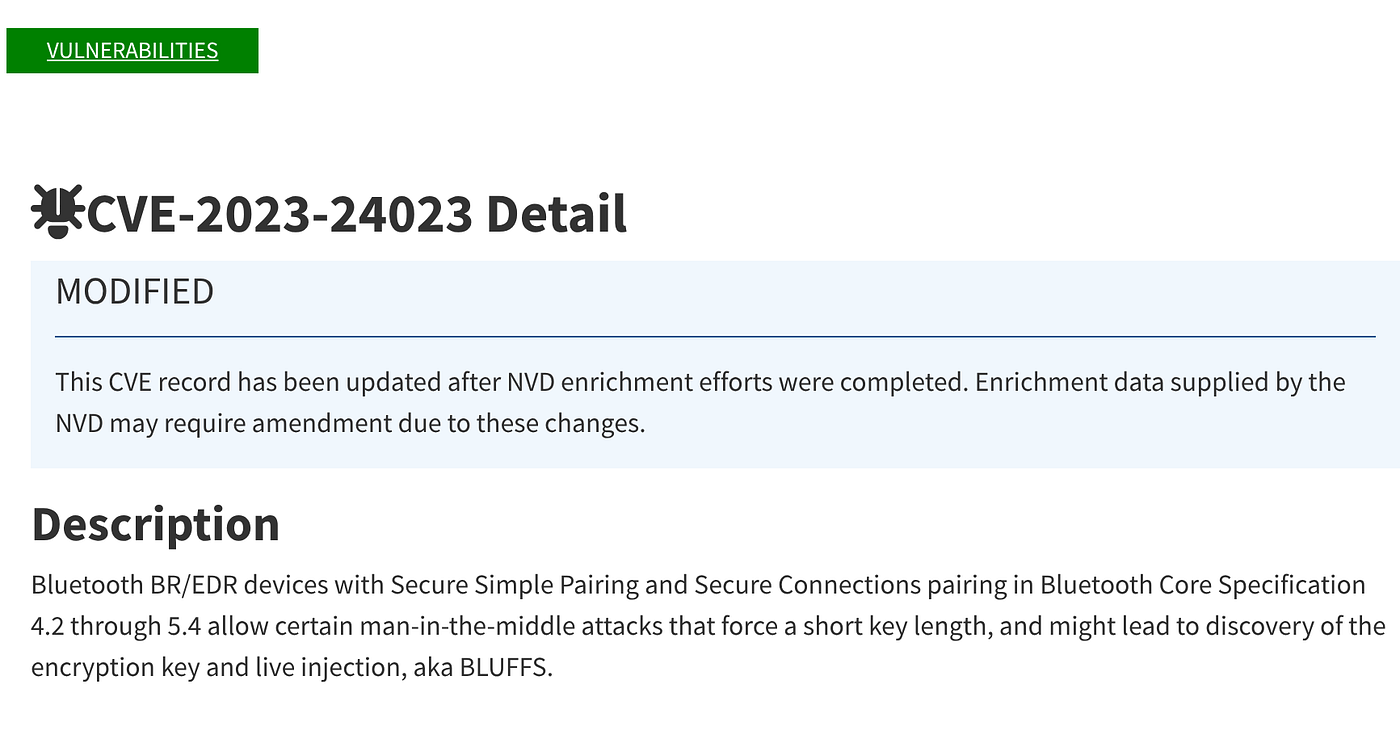
Bluetooth Tools
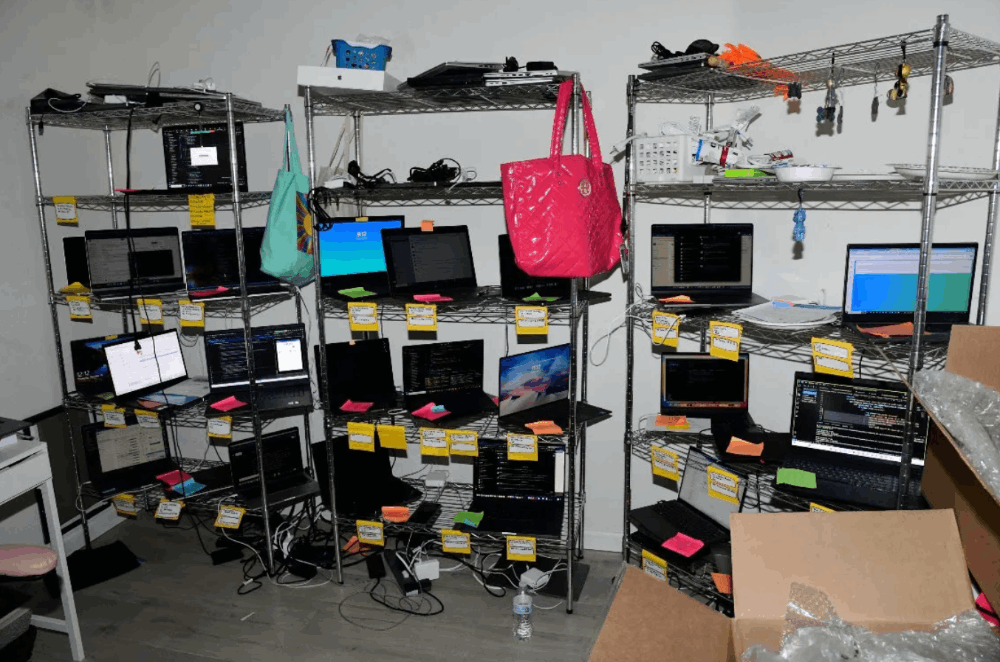
The tools you might like to use to investigate the Bluetooth stack will usually vary according to the type of research you are looking to carry out. Typically, you’ll want a mixture of both hardware and software-based tools to ensure you’re covering all bases, and if you’ve read the publication for a while, you probably will recognise some familiar names that we’ve covered before.
Wireshark and Kismet can give you software solutions for capturing Bluetooth packets, identifying MAC information and capturing BLE packets. For detailed analysis and reproduction, Universal Radio Hacker and Inspectrum allow for both capture and reproduction of signals of interest and examination of the IQ data within a capture.
At the hardware level, Great Scott Gadgets provides several useful tools, including the Ubertooth One and the Hack RF Portapack. Better described as a combination system that covers both hardware and software, both systems are used for the capture of signals and out-of-box reproduction of certain attack vectors.
If neither of these solutions takes your interest, it’s worth remembering that the Flipper Zero can also be used for Bluetooth research, while the purchase of a decent Bluetooth module or dongle allows for the building of all sorts of custom devices thanks to the magic of GitHub.
Already running Linux and want to have a quick look using hardware you already own?
Try this command to run a long-duration scan to discover devices within your local area. Take your laptop somewhere busy to find even more data.
# Run long-form scan sudo btmon > bluetooth_sweep.log & # Let run for 30-60 minutes
Wireless Hygiene
In modern security circles, there are plenty of clickbait articles that are designed to induce hype regarding the usage of Wi-F networks and insecure Bluetooth protocols. While this might have been true in the past, a strong focus on wireless security over the past few years has meant that for the average user, the level of risk has dropped dramatically.
Unique admin passwords, better network encryption and the standardisation of HTTPS mean that much of the old school information that left many people fearful of using public networks, simply isn’t relevant today.
However, there are some steps you can take to sanitise your wireless footprint with regard to tracking and privacy, and one of the biggest is simply ensuring that you switch off broadcasting if this is something that is a concern for you.
Privacy-focused operating systems like Graphene OS will normally use emissions control strategies out of the box. While you may not be interested in making the shift to a privacy-focused OS, having an understanding of how to reduce your wireless footprint can still be a smart practice if you have concerns regarding privacy.
Like most things in life, considerations regarding security will often have to navigate the line between convenience, ease of adoption, and real-world usage.
The most secure option is usually not the most convenient, and making decisions that balance out these often conflicting values is usually why experienced information security wizards can command the big dollars.
Investigator515 explores the RF spectrum, cybersecurity, and the hidden tech behind modern espionage.
Follow for new content weekly
Bluesky • X • Substack
You might also like,
- OSINT Investigators Guide to Self Care & Resilience
- Spies In The Mud: The RF-111 Aardvark
- What The Tech?! Space Shuttles