Modern Espionage: The IT Worker Scam
Fake workers earn revenue to bypass sanctions and treat data theft as an extra perk.
As we’ve developed the Silent Wars publication, we’ve taken a look at several historical and Cold War-era espionage incidents that would play a key role in times of global uncertainty.
These are interesting to read and write about, but they don’t touch on the fact that in today’s post-COVID world, state-backed espionage is more prevalent than ever. And, thanks to modern technology, there are now plenty of ways for intelligence agencies to approach this.
So, we’re going to mix it up a bit in the future with the occasional coverage of more modern espionage operations, and today, we’ll be kicking it off by looking at the IT worker scam.
Helping to bypass financial sanctions while earning hard currency and opening up the door to possible data exfiltration, it’s an extremely lucrative scam that would be helped along the way by our reliance on remote work during COVID-19.
Let’s go take a look!
Background
The internet has been around for ages now, but for countries like North Korea who had low connectivity rates, it would take a significant shift for this to be leveraged for state-backed purposes.
Initially, the push would come in the early 2010s as new leader Kim Jong Un would take over North Korea. Educated in the West, Kim Jong Un would be a known fan of technology, having been exposed to plenty of it during his time at school.
It’s fair to say that North Korea had somewhat of a limited tech scene prior to this. While computers did exist, they were used by the upper parts of society and more often than not, ran highly monitored Linux distributions like Red Star OS that helped to ensure censorship and tracking capabilities weren’t compromised.
The new leader would promote a heavy technological shift as the country would continue its slow march towards being a nuclear power. With nuclear weapons playing a key role in ensuring the safety of the regime, this new push towards technology would help generate specialists who could go on to work on parts of the regime’s nuclear weapons program.
Like most countries in the world, IT specialists and hackers would play a key role here, spearheading some of North Korea’s most ingenious cyberattacks and helping to establish cybercrime as a key stream of revenue for the North Korean government.
It would be 2014 when the cybercrime campaigns would really start to ramp up their operations, and it would be as ingenious as it was effective.
Using fake identities, North Korean IT specialists would approach American companies for employment. Once they had landed a job, they would be earning hard currency that would be funnelled back to the regime with the added bonus of being able to peruse proprietary data at their leisure and, if suitable, extract that data for commercial purposes.
Obviously, the “Honest Work” meme does not apply here.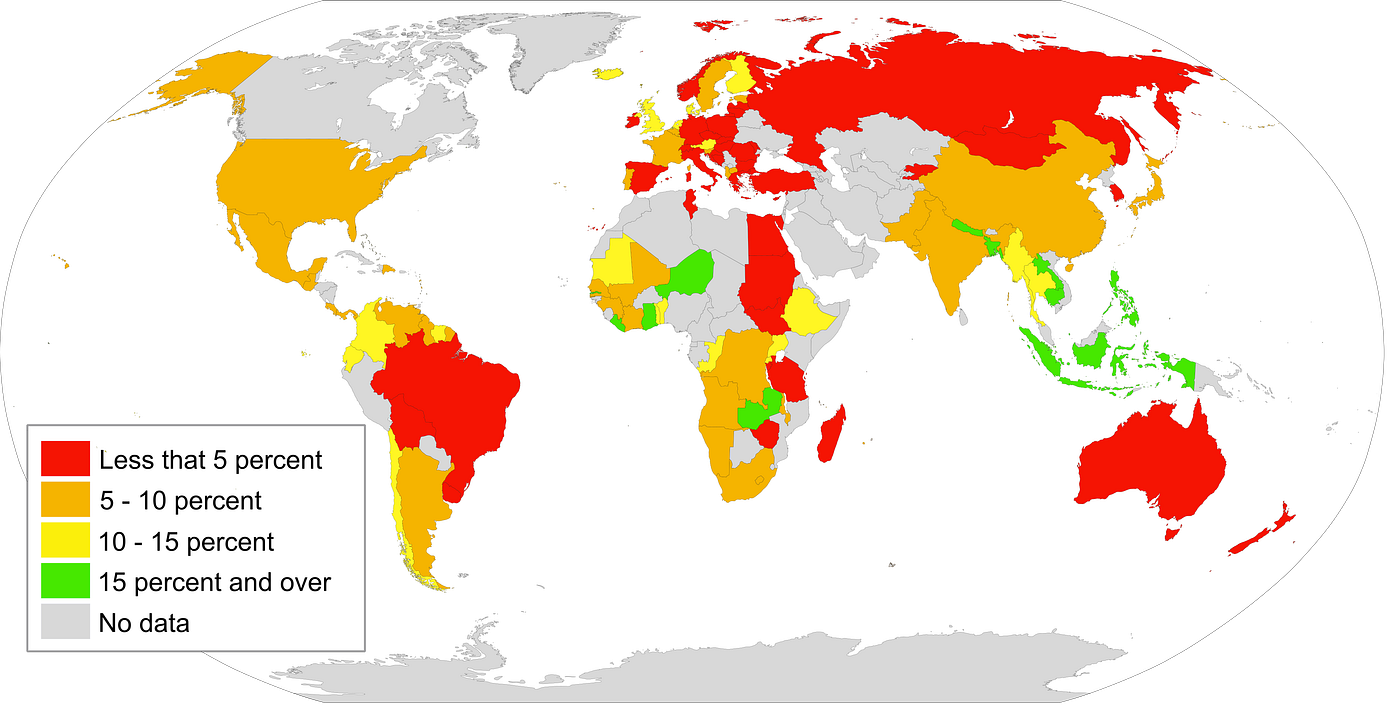
Traitors On The Inside
While the process appeared relatively simple at the surface level, the reality was that most US companies had measures in place to ensure someone was who they said they were and where they said they were.
To bypass most of these processes, the North Korean workers would simply recruit people within America to act as middlemen. Once recruited, they’d send the middleman some hardware, which they’d log into remotely, giving them an American IP address and hardware that matched the expected configuration.
It’s worth pointing out that this was no small operation, as thousands of IT specialists have been linked to the operation over the years. More worringly for the Americans, there seemed to be no end to the list of people willing to act as middlemen, either. Over the period 2016–2022, multiple laptop farms had been exposed, with willing US citizens at the helm.
The capture of these farms would also help to fill in some of the gaps regarding the effectiveness and strategies of the operation. With several large-scale farms caught literally red-handed, investigators would link more than 40 million dollars to the operation in just the data they had. This belied the true scale of the operation, however, as the expected haul is to be in excess of 250 million in revenue per annum, which is no small amount.
It would also help expose the usage of Deepfakes and other modern technology tools that were being used to fool interviewers and ensure that the illegal IT workers were often able to stay one step ahead of the game.
Who Was Affected?
With the revenue levels involved, it’s easy to understand that this was lucrative, but it might surprise you to learn just how deep this scam would end up going.
Multiple Fortune 500 companies would be exposed as targets, and interviews with information security specialists would reveal that most of them had had experience as targets of the scam.
It would also show that while the scam originally targeted America, the success of the operation had meant that it had started to migrate to Europe as well. The United Kingdom, Romania and Poland would all report uncovering similar schemes within their borders as well.
It’s worth pointing out that while the scam is reasonably low-tech, it was given a very distinctive helping hand in itsit’s success thanks to the evolution of the COVID-19 pandemic. As large parts of the world would undergo lockdown in an attempt to control the spread of the virus, reliance on remote work would skyrocket.
This would give the North Korean teams an additional helping hand in their operations, making it much, much easier for the teams to land the paid positions they needed to carry out their espionage work.
Blockchain Backed Weapons Programs
With North Korea a fully fledged nuclear power, it’s fair to say that in a lot of instances, the remote IT worker scam has more than met its goal. While the arsenal of weapons remains small in comparison to China, Russia or the United States, the North Korean regime still has access to multiple weapons that have increased its overall security posture.
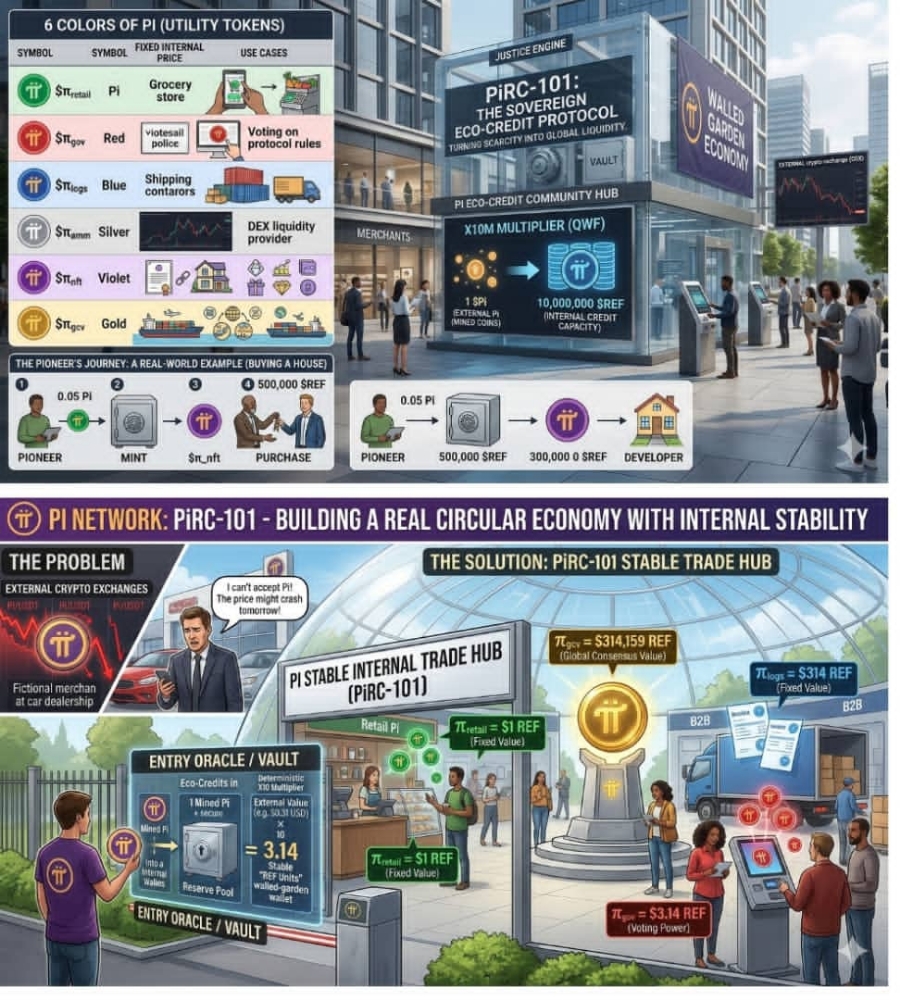
And here, close to the end, we get to the strangest part of the tale. Namely, the usage of cryptocurrencies for sanctions evasion.
While cryptocurrencies are a controversial technology in their own right, clear links have been established between the technology and multiple regimes using it for sanctions bypassing. It wouldn’t just be the usage of crypto either, as North Korean hackers would deliberately run cryptocurrency scams in an attempt to steal assets as well.
This is, in my opinion, one of the most interesting takes regarding the whole remote worker scam in general. It doesn’t link to a single espionage incident. Instead, it helps to highlight an entire pattern of behaviour that, when carried out over years, proved to be devastatingly effective in terms of the revenue raised, the information that was stolen and where the dark money ended up at the end of the trail.
We sure do live in interesting times.
Investigator515 explores the RF spectrum, cybersecurity, and the hidden tech behind modern espionage.
Follow for new content weekly
Bluesky • X • Substack
You might also like,
- Your First SIGINT Toolkit For Under $100.00
- Hidden Trackers: 5 Ways Your Tech Betrays You
- The Night Stealth Fell: The Story Of Vega-31