What The Tech?! Tor Network
A US naval research lab project, TOR would change the dynamic around privacy vs surveillance.
In recent years, TOR has taken more than a few hits. Touted as a tool for criminals, drug dealers and those who both live and play on the darknet, the original reasons for the development of TOR have long since left the limelight.
If you’re not a nerd, however, the actual development of TOR might surprise you, given its current use case. Not only was TOR developed by a government agency, but it was developed as a means of securely transferring information.
While it looks a little different today than it did back at the start, it’s still a key feature in our modern world.
Let’s go check it out!
History & Development
If you’re of the younger generation, you probably won’t remember the Crypto Wars that took place in the mid to late 90s. Here, privacy would be a hot-button issue and similar to today’s world, the battle lines would remain relatively similar.
There was a government that would deem itself to have a need for “clear and unrestricted access” via backdoors, while the rest of society was typically subscribing to the “hell no” school of thought. While this battle would pertain to a so-called “clipper chip” that enabled backdoor access, the reality was that, thanks to the newfangled interwebs, privacy in general was now a hot topic across the board.
While telecommunications and radiocommunications had their issues around security, these were tested methods that were reliable and well understood, meaning that while privacy was sometimes a compromise, it would never be sacrificed entirely.
Being relatively new, the internet had no such protections. And so, in the mid 1990’s, it would be the job of the US Naval Research Academy to identify ways and means with which the internet could be used as a secure means of communication for spies, intelligence analysts and other government workers.
This would involve analysis at a metadata level. If you’ve spent any time around networking, you’ll know that this metadata is included at the packet level, and it gives clearly identifying attributes that are able to be used for identification purposes.
The Americans aimed to develop methods to circumvent all of this, which would leave them with the backbone of the internet being a perfectly functional, yet fully anonymous, high-speed communications tool. This was no small ask, and doing so successfully would result in an incredibly useful tool for spies and intelligence assets.
The Original Prototype
The Navy would come up with the original onion routing protocol in the mid to late 1990’s as it tested new methods of achieving the same goal.
The idea was as simple as it was ingenious. Rather than treating the internet as a point-to-point system where servers would communicate directly to exchange information, Onion routing would use relay nodes provided by middlemen to steer their connection away from its point of origin.
Each system would use multiple hops through these relay nodes to obfuscate the client from the server, providing some level of anonymity to the end user.
This theory worked pretty well in a test environment; however, it was soon realised in 1997 that for the system to work most effectively, it would need to carry other traffic to provide cover for the spies. And so, the Onion Routing protocol would be finalised in the following capacity before being opened to the public. Here’s how it worked.
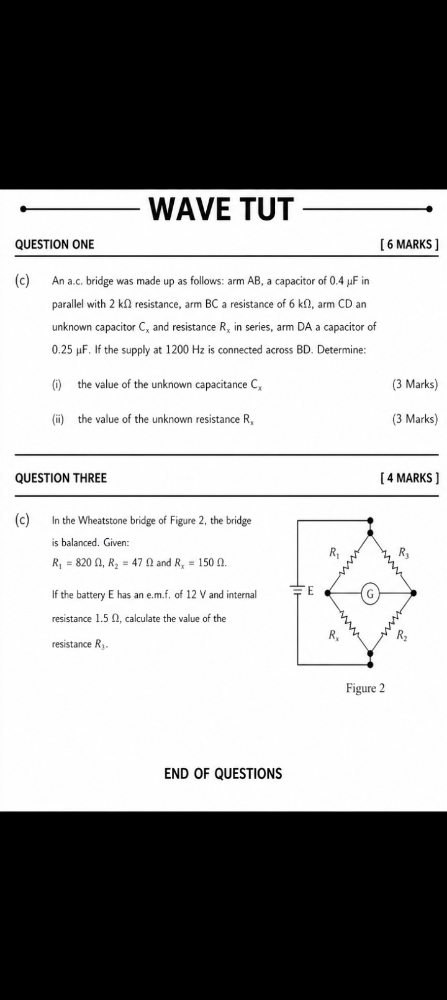
Three-layer encryption (“onion”) through three random nodes means:
- Entry node: knows WHO you are, not WHERE you’re going
- Middle node: knows neither
- Exit node: knows WHERE you’re going, not WHO you are
No single point knows both ends. Beautiful. And more importantly, Simple.
Usage In the Modern Day
While the early research would focus on the routing protocol, further development would eventually give us the TOR browser, the tool with which most people typically access the dark web.
However, unlike most stories where we take a look at the technical components that took us on this journey, for TOR, the most interesting part is the social fabric that would bring everything together to create the dark web as we know it.
While onion routing was some pretty cool technology, the focus on usage by spies and intelligence assets gave the US government a unique, but very real problem. Adversaries might not be able to decode the traffic, and they might not know where it was going. But if traffic was present on the network, it was reasonable to assume that it would be from spies or intelligence assets, and this posed a problem.
So here, the question of “Why is TOR available to the public?” can now be answered. Because filling the network with ancillary traffic by reporters, activists and other TOR users gave the intelligence community, who were the original users of TOR, extra cover to hide amongst.
This is the very definition of hiding in plain sight, a surveillance strategy that is far older than the development of computers and one that still works quite well, even today.
While TOR has been controversial and attracted intense criticism for its role in things like the Silk Road market, it started with, and continues to obtain large amounts of funding from the US government. While it has dropped over the years, from about 80% in 2012 down to around 35% in 2024, it does leave the government in the unique position of paying for the tools that help to protect people from them
An Intelligence Agencies Playground
This wouldn’t be the only unique position for the US government with regard to TOR. Later years would see the government starting to attack the network after it had become too much of a good thing.
While the CIA would launch a website and remain active on the network, the Snowden era revelations would incense the National Security Agency, which would then put in significant work with regards to deanonymizing TOR users.
With the release of a slide paper called “TOR Stinks”, the agency would acknowledge that it was impossible to break the protocol overall and as such, it was deemed more productive to target specific computers and nodes within the TOR network.
It wasn’t just the NSA trying their luck, though. The proliferation of illicit drugs and services on the darknet would see law enforcement agencies leveraging TOR for privacy purposes while putting in significant effort to track holders of cryptocurrencies, onion websites and other TOR users.
While the original TOR protocol remains secure, the proliferation of compromised nodes and longevity in carrying out investigations mean that in today’s world, anonymity is no longer a certainty like it was in the earlier days.
A Peculiar Problem With Anonymity
To highlight this, we need to look no further than the case of Eldo Kim. A student at Harvard in 2013, Kim would be unprepared for his final exams when he would elect to place a bomb threat to the college in an attempt to gain extra time, thanks to his threats.
He’d use the TOR network to place his complaint, however, due to traffic analysis, he would be caught and placed under arrest within 24 hours of placing the threat.
His problem? He would access TOR via the Harvard network, and it was this traffic that law enforcement was able to identify. They didn’t need to break the TOR protocol, the fact that Kim was the only person on the Harvard network at the time using it was enough to identify him.
Privacy really can be a variable sometimes.
Investigator515 explores the RF spectrum, cybersecurity, and the hidden tech behind modern espionage.
Follow for new content weekly
Bluesky • X • Substack
You might also like,
- OSINT Investigators Guide to Self Care & Resilience
- Spies In The Mud: The RF-111 Aardvark
- What The Tech?! Space Shuttles