The Evolution of Cyberattacks in Cyberspace
Cyberspace: A Notional Environment with Real Challenges and Risks
Cyberspace is the online world of computer networks and especially the Internet. It is a notional environment in which communication, interaction, and exchange of information take place through digital technology. Cyberspace has become an integral part of various aspects of human life and activity, such as economy, culture, politics, and security. However, cyberspace also poses significant challenges and risks, as it is vulnerable to cyberattacks by malicious actors who seek to disrupt, damage, or exploit critical systems and sensitive data.
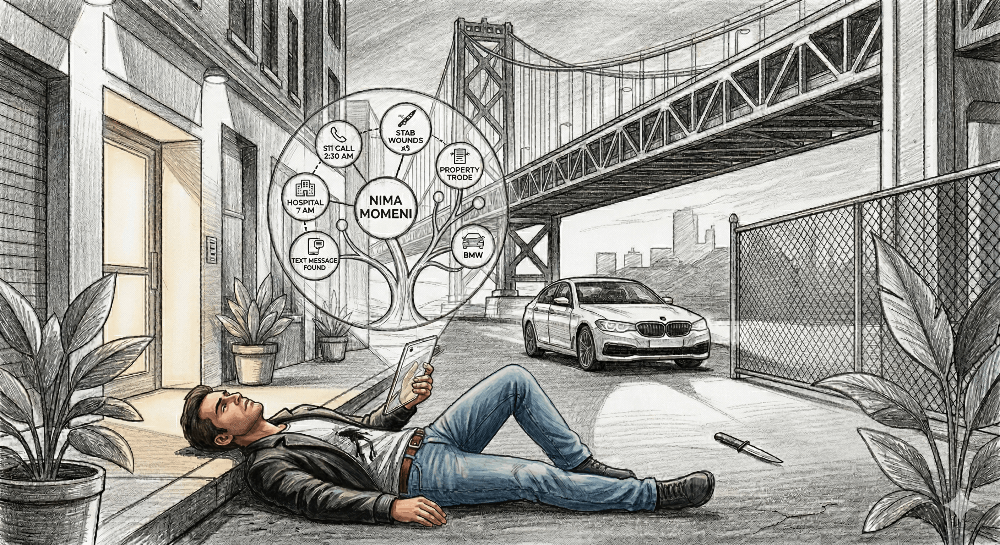
Cyberattacks are premeditated attacks or threats of such attacks by nonstate actors intending to use cyberspace to cause physical, psychosocial, political, economic, ecological, or other damage. Cyberattacks can have different types, methods, targets, and consequences depending on their goals and techniques. Some examples of recent cyberattacks are the SolarWinds hack that compromised several US government agencies and private companies in 2020, the Colonial Pipeline ransomware attack that disrupted fuel supply in the US in 2021, and the Microsoft Exchange Server hack that affected hundreds of thousands of organizations worldwide in 2021. In this post, we will explore the concept of cyberspace and the types of cyberattacks that occur in it. Let’s take a look at how cyberattacks have evolved over time and what are some of the best practices and technologies for preventing and mitigating them.
The Evolution of Cyberattacks
Cyberattacks have changed over time in terms of methods, targets, and sophistication. Since the late 1980s, cyberattacks have evolved several times to use innovations in information technology as vectors for committing cybercrimes. However, traditional cyber threats such as viruses, worms, and denial-of-service (DoS) attacks remain as the source of the most common attacks.
The first decade of the new millennium saw more advanced persistent threat actors (APTs), most of which were sponsored by nation-states. The evolution of cybercrime meant new viruses and worms, which caused significant damage to critical sectors of the global digital economy. Some examples of these attacks are the Stuxnet worm that sabotaged Iran’s nuclear program in 2010, the Shamoon virus that erased data from Saudi Aramco’s computers in 2012, and the WannaCry ransomware that infected hundreds of thousands of computers worldwide in 2017. In recent years, cyberattacks have become more complex and diverse, involving multiple stages, techniques, and actors.
Some emerging trends and challenges in cybersecurity are:
- The use of artificial intelligence (AI) and machine learning (ML) by both attackers and defenders to automate tasks, enhance capabilities, and evade detection.
- The rise of cyber espionage and information warfare as tools for gaining strategic advantage, influencing public opinion, and disrupting adversaries.
- The proliferation of Internet of Things (IoT) devices and smart systems that create new attack surfaces and vulnerabilities.
- The increase of supply chain attacks that compromise third-party vendors or software components to gain access to target networks or systems.
- The expansion of ransomware attacks that encrypt data or disrupt operations until a ransom is paid, often targeting critical infrastructure or public services.
Types of Cyberattacks
Cyberattacks can be classified into different categories based on their goals, techniques, and effects.
Some common types of cyberattacks are:
- Data breaches: Unauthorized access to or disclosure of confidential or sensitive information, such as personal data, financial records, trade secrets, or intellectual property.
- Malware: Malicious software that infects a computer or system to perform unwanted or harmful actions, such as stealing data, deleting files, encrypting data, displaying ads, or spying on users.
- Phishing: Fraudulent emails or messages that trick users into clicking on malicious links or attachments, or providing personal or financial information.
- DoS/DDoS: Denial-of-service or distributed denial-of-service attacks that overwhelm a server or network with traffic or requests to disrupt its normal functioning or availability.
- Man-in-the-middle (MITM): Attacks that intercept or alter the communication between two parties without their knowledge or consent, such as eavesdropping on messages, modifying transactions, or redirecting traffic.
- SQL injection: Attacks that exploit a vulnerability in a database-driven website or application by inserting malicious SQL commands into user input fields, such as login forms or search boxes.
- Zero-day: Attacks that exploit a previously unknown vulnerability in a software or system before it is patched or fixed by the vendor or developer.
- Cryptojacking: Attacks that use a victim’s computer or device to mine cryptocurrency without their consent or knowledge, consuming their resources and affecting their performance.
The Prevention and Mitigation of Cyberattacks
Cyberattacks can cause significant losses and damages to individuals, organizations, and nations. Therefore, it is essential to adopt effective measures and technologies for protecting critical systems and sensitive information from digital threats.
Some best practices and technologies for enhancing cybersecurity are:
- Encryption: The process of transforming data into an unreadable format using a secret key or algorithm to prevent unauthorized access or modification.
- Authentication: The process of verifying the identity of a user or device before granting access to a system or service using methods such as passwords, biometrics, tokens, or certificates.
- Firewall: A software or hardware device that monitors and filters incoming and outgoing network traffic based on predefined rules or policies to block unwanted or malicious connections.
- Antivirus: A software program that detects and removes malware from a computer or system using signatures, heuristics, or behavioral analysis.
- VPN: A virtual private network that creates a secure and encrypted connection between a user’s device and a remote server over a public network such as the Internet.
- Backup: The process of creating copies of data or files and storing them in a separate location or medium to ensure their availability and recovery in case of loss or corruption.
- Patching: The process of updating software or systems with the latest versions or fixes to address vulnerabilities or bugs.
A Comprehensive and Proactive Approach to Cybersecurity
In this post, we have explored the concept of cyberspace and the types of cyberattacks that occur in it. We have also looked into how cyberattacks have evolved over time and what are some of the best practices and technologies for preventing and mitigating them. Cyberspace is a vital and dynamic domain that offers many opportunities and benefits for human society, but also poses significant challenges and risks for security and privacy.
Cyberattacks are diverse and complex phenomena that can cause serious losses and damages to individuals, organizations, and nations. Therefore, it is essential to adopt a comprehensive and proactive approach to cybersecurity that involves awareness, education, collaboration, innovation, and regulation. By doing so, we can enhance our resilience and readiness to face the current and future threats in cyberspace.
References and Sources
- Plotnek, J., & Slay, J. (2016). A taxonomy of cyber terrorism. In Cybercrime and Cloud Forensics: Applications for Investigation Processes (pp. 1-18). IGI Global.
- Merriam-Webster. (n.d.). Cyberspace. In Merriam-Webster.com dictionary. https://www.merriam-webster.com/dictionary/
- Wikipedia. Cyberattack. In Wikipedia, The Free Encyclopedia. https://en.wikipedia.org/w/index.php.title=Cyberattack&oldid=1022959730
- Popescu, M., & Dascalu, M. I. (2015). Trends, patterns and security countermeasures in network vulnerabilities and attacks: A survey of the last decade. Procedia Economics and Finance, 28, 97-103.
- Arctic Wolf. (n.d.). Decade of cybercrime: The evolution of cyberattacks from 2010 to 2020. https://arcticwolf.com/resources/blog/decade-of-cybercrime/
- Center for Strategic and International Studies. (n.d.). https://www.csis.org/programs/strategic-technologies-program/significant-cyber-incidents
- IBM. (n.d.). What is a cyberattack? https://www.ibm.com/topics/cyber-attack