Cyber in Space: A New Era Requires A New Strategy
Space is fast becoming the new frontline for in-orbit cyberwarfare
As part of the Radio Hackers publication, we’ve spent plenty of time examining and discussing Cybersecurity in space-based assets. With security by obscurity the default approach for much of the past, it’s clear that now, not only is this attitude shifting, but it has, in fact, been dead for some time.
While there’s been plenty of things to help substantiate this fact, we can point to a couple of different incidents that would help to lay the foundations for this new age. Firstly, Russia’s invasion of Ukraine would help to show the importance of smart spectrum management, while the importance of systems like Starlink to modern warfare is obvious to anyone who’s spent more than a passing few minutes observing or analysing the conflict.
Government assets require government security, and more importantly, collaborative programs require collaborative approaches. So, when the governments of Australia, New Zealand, Canada & the US drop a paper on securing assets in low-earth orbit, you just know it’s going to be a good read.
Thankfully, we’re going to read it so you don’t have to!
On the off chance you want to, though, visit this link. Kinetic satellite attacks have been around since the 80’s era ASM-135 ASAT. The threat pictures looks much, much different now. Source: Wikipedia
Kinetic satellite attacks have been around since the 80’s era ASM-135 ASAT. The threat pictures looks much, much different now. Source: Wikipedia
The CIA Triad
Space can be hard, but some cyber folk might be a little surprised to realise that the same rules that dictate how we operate and what we do on Earth can often apply to the space-based assets as well.
While Kinetic methods for dealing with assets in space have long existed, the proliferation of modern technology now means that it’s trivial for an adversary to profile, enumerate and attack space-based assets.
So, while kinetic attacks have existed since the 80’s, they’ve become less relevant with the passage of time and the development of new strategies. This is even more so when we consider the consequences of the Kessler effect and the in-orbit consequences of satellite debris. Now, there’s plenty of motivation to attack and pwn a Satellite without creating a debris field that affects everybody.
So, it’s no surprise that one of the first things mentioned in the doc is the CIA Triad.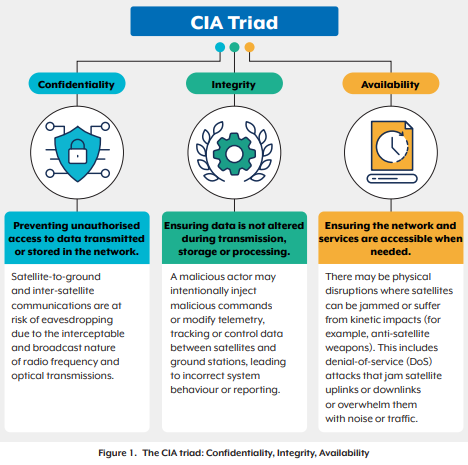 The triad will be familiar to those who are already involved in cyber/info sec. Source: asd.gov.au
The triad will be familiar to those who are already involved in cyber/info sec. Source: asd.gov.au
Before you ask, no, this doesn’t refer to a certain government-backed intelligence agency.
Instead, it refers to Confidentiality, Integrity and Accessibility, three key metrics that help define the importance of some core information security goals.
While most information security folks should have a clear understanding of the triad, if you’re new to this, here’s a closer look at what it all means.
Confidentiality: Ensuring that only authorised people can access or view the information.
Integrity: Trusting that the data that is presented is accurate and has not been compromised.
Availability: Ensuring the system remains up and available when needed.
To make this easier to understand, let’s put it in a context that most people use and can understand. Namely, the usage of internet banking services.
Confidentiality: No one else can see your account details or transfer money.
Integrity: The balance shown is correct, and transfers actually happen as intended.
Availability: The app works and is accessible 24/7, so you can pay bills on time.
If a hacker steals your data, then confidentiality is broken. If a hacker changes your account balance, then integrity is broken. Lastly, if the bank’s servers crash and you can’t access your account, then availability is broken.
It’s worth mentioning that, in terms of building blocks, the triad is simply the foundation. Almost every security control, policy, or technology you’ll learn about is designed to protect at least one (and often more than one) of these three pillars.
Because of this, you’ll also see the triad play a key role in industry standard certifications, like NIST. It’s also fair to say that the triad looks a little different when it’s orbiting the Earth at 27,000 km/h.
The Overlap With Traditional Cyber
Space is unique in that while it has plenty of cutting-edge technology available in-orbit, it’s also uniquely vulnerable to measures that have been substantially mitigated here on Earth. It also changes the threat picture that we might expect to see target space-based assets.
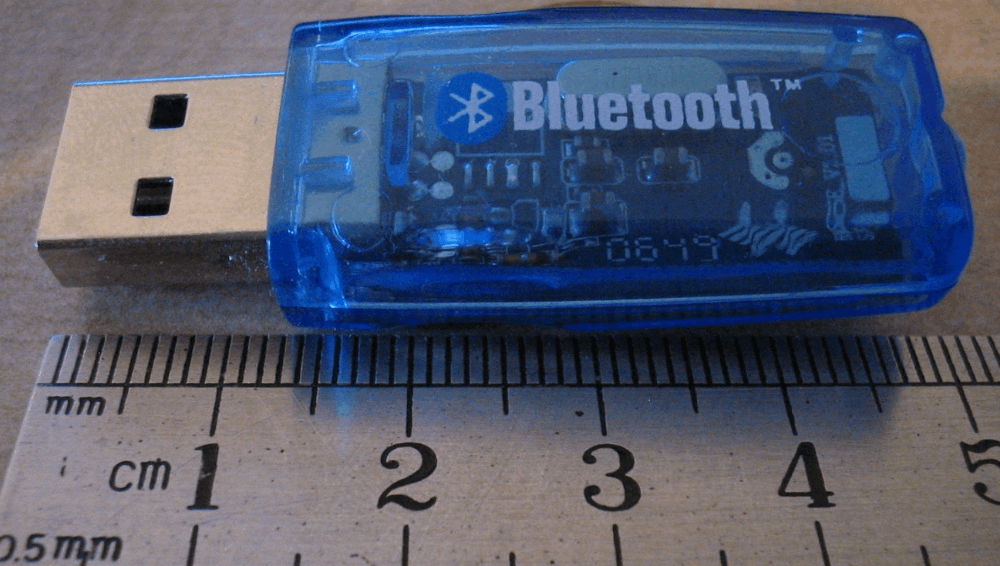
Wireless communication, by its very design, comes with some inherent needs that, in the right circumstances, can easily be exploited. And, it’s these exploits that the ASD handbooks aim to mitigate.
For instance, the requirement for satellites to be accessible by a ground station and be able to accept new commands means that a simple jammer can apply a basic denial of service attack on the uplink frequencies. While this wouldn’t cause a problem for users on the downlink, it would prevent the system from being updated or re-tasked.
Spoofing and replay attacks are also extremely relevant attack vectors to space-based systems. While on Earth, it’s common to use rolling codes and other strategies to help prevent these types of attacks, in-orbit assets traditionally haven’t had these types of protections available to them in the past. The unique requirement to interact with ground stations also creates a dynamic where these attack vectors can be much, much different in comparison to how we would assess them on Earth.
Thankfully, the evolution of technology means that this is now slowly changing, and it’s technological shifts that the ASD makes mention of in this document.
While it’s hard to apply a single strategy to solve everything at scale, modern inventions like beamforming, frequency agile systems, and modern, cryptographic session keys make it much easier to help identify and address these problems when they occur.
It will not solve every problem. But it will help us to apply fixes and help increase the security posture of assets that may have been built in an era where the risk of these types of attacks was much lower. This is even more prevalent when discussing the concept of nation-state cyberattacks in space.
A Peculiar Problem
The more things change, the more they stay the same, and this brings us to another unique problem that we often see here on Earth, too. Namely, the use of hardware that has lived and operated far beyond its original lifecycle.
To consider this issue, we’ll take a quick look at AMSAT’s AO-7 satellite.
Known as Amsat Oscar 7, AO-7 is one of the oldest operational satellites in any capacity. Being launched in 1974, it’s no lie to say that often, the satellite is far older than the radio amateurs who operate it, and with this maturity comes a few unique security considerations.
With a mass of around 28kg and capable of carrying and operating a large, radiofrequency-based payload, AO-7 would provide reliable service to amateurs worldwide. It would also be responsible for testing and validating satellite-satellite links, a task that it would successfully complete early in its life cycle.
However, it's this RF payload that would ultimately cause issues. With AO-7 launching in the early 70’s, it’s fair to say that the spectrum looked pretty different back then in comparison to now. As the global regulator would look to apply uniformity to space-based systems, 1979 would see some significant changes in how the spectrum would be managed. Unfortunately for AO-7, this would now mean that part of its RF-based payload would be operating “out of band”.
While a simple waiver would help to solve this issue, it’s a clear indicator that sometimes, problems can come from unexpected places. While AO-7 was a popular satellite among amateurs, you don’t have to be a rocket scientist to realise that a satellite orbiting the globe while transmitting out of band has the potential to cause some pretty significant interference issues. It also helps highlight some unique security vulnerabilities that come with orbital assets.
AO-7 would have one more piece of gold to contribute to the conversation, however. In 1981, after more than seven years of service, a failure in its NiCad battery would see the satellite “go down” and become inaccessible to radio amateurs.
In 2002, however, things would change as radio amateurs would identify signals that appeared from AO-7’s beacon as it appeared overhead. Transmitting the traditional AMSAT “hi hi” greeting in Morse code on the satellite's VHF transmitter, something had clearly happened to AO-7 to bring it back to life.
Ultimately, it was deemed to be a rare “open circuit” within the battery that enabled AO-7 to start working again in complete sunlight.
While this would be great news for radio amateurs, it would provide an interesting quandary for governments, satellite builders and commercial operators.
Because, as you’d imagine, a nearly thirty-year-old dead satellite coming back to life is going to cause all sorts of logistical surprises.
Despite being an amateur satellite, the lesson here would be clear. With hardware often working far beyond its expected lifespan, it’s pretty clear that something designed with a 1970s-era security posture simply isn’t going to cut it in the modern age.
The fact that this is an in-orbit asset also means that, for obvious reasons, turning it off, servicing it, modifying it, or changing it has to be done remotely or alternatively, can’t be done at all.
Opinions: We All Have Them
Let’s be entirely clear. Documents like this, released by governments, have the potential to make things much, much easier for operators and those who access such systems.
Cyber can be hard. Space can be hard. Any resources that increase a security posture while making it easier for end users to understand can only be a good thing.
If you want confirmation of the changing dynamic of space, here’s an interesting quote that helps to summarise this perfectly.
“These factors demand specialised security approaches that go beyond conventional terrestrial models. These approaches must protect against space-specific threats such as spoofing, signal degradation and compromised ground stations.” (Page 5)
It gets better, though. With supply chain attacks making all sorts of headlines in recent years, the document stresses the importance of managing these risks as well. In fact, not only do they mention it as a risk factor, but it’s covered in some pretty extensive detail as well.
“The supply chain for LEO SATCOM systems usually spans multiple vendors and subcontractors. It introduces risks such as hardware and software backdoors, tampering during manufacturing, and insertion of counterfeit components. The complexity and global nature of the supply chain make it difficult to ensure consistent security practices.” (Page 6)
While people naturally draw differing conclusions on these matters, for the most part, it helps to highlight one key point around space-based assets. What was once an out-of-sight, out-of-mind, black box system is now an integrated node in a distributed network, playing a critical role.
With on-board processing, inter-satellite communication links and the potential for Artificial Intelligence to be added into future designs, satellites aren’t just dumb relay systems anymore.
The deep integration into modern systems provides a unique security landscape challenge that is complicated further by the constantly moving nature of space-based assets and a huge reliance on the information that these systems produce.
Some might claim that wireless security has little to do with traditional cybersecurity postures.
The reality is that the spectrum becomes more important and the overlap grows with each new technological shift.
What are your thoughts on this?
Investigator515 explores the RF spectrum, cybersecurity, and the hidden tech behind modern espionage.
Follow for new content weekly
Bluesky • X • Substack
You might also like,
- OSINT Investigators Guide to Self-Care & Resilience
- What The Tech?! Water Purification
- Radio Hackers: Bluetooth Security