Cybersecurity Trends 2024
Photo by GuerrillaBuzz on Unsplash
To protect ourselves and our valuable information effectively, we must remain vigilant and informed about the emerging trends and developments in the cybersecurity landscape.
With that in mind, we are excited to explore the top cybersecurity trends anticipated to shape the industry as we move forward into 2024.
1. Artificial Intelligence in Cybersecurity
The influence of Artificial Intelligence (AI) on various industries has been substantial, and its impact on Cybersecurity continues to grow. Looking ahead to 2024, we can anticipate AI playing an even more prominent role in mitigating cyber threats.
AI in Cybersecurity | IBM
AI-powered systems can analyze vast amounts of data, detect anomalies, and identify potential vulnerabilities in real time. By leveraging machine learning algorithms, AI can continuously adapt and improve its ability to identify and respond to new threats.
2. Zero Trust Architecture
Traditional security models often relied on perimeter-based defenses, assuming all users and devices could be trusted once inside the network.
With the rise of sophisticated attacks, relying solely on perimeter security is no longer sufficient. Zero Trust Architecture (ZTA) is a security framework that assumes no trust by default.
Overview of Zero Trust Architectures
It requires strict authentication and authorization for every user and device accessing network resources.
As we look ahead to 2024, it is predicted that ZTA will experience a significant surge in adoption among organizations. This can be attributed to the growing realization of the need to fortify their security posture.
3. Quantum Computing and Cryptography
While quantum computing can potentially revolutionize various industries, it poses a significant threat to cryptographic algorithms. Quantum computers can break many encryption algorithms that currently secure digital communications and data.
Quantum Computers, Explained With Quantum Physics
Researchers are developing encryption methods resistant to quantum attacks to prepare for this potential threat.
By 2024, we anticipate a greater focus on post-quantum cryptography and adopting secure encryption algorithms against quantum computing.
4. Internet of Things (IoT) Security
The proliferation of IoT devices has created new avenues for cyber attacks. From smart homes to industrial control systems, the security of IoT devices remains a significant concern.
2024, we anticipate an increased focus on IoT security as more devices become interconnected.
This includes implementing robust security measures such as strong authentication, secure firmware updates, and network segmentation to isolate compromised devices.
5. Cloud Security
The migration of infrastructure and services to the cloud is becoming more prevalent, emphasizing the significance of ensuring cloud environment security.
Anticipated advancements in cloud security technologies and practices in 2024 will further enhance this aspect.
Today's Cloud Security Problems Are the Same as Yesterday's
This includes improved identity and access management, data encryption at rest and in transit, and enhanced monitoring and detection capabilities.
Moreover, as organizations look to enhance security and segregate workloads, there is a rising demand for containerization and serverless computing models.
6. Privacy Regulations and Compliance
Governments across the globe have responded to the growing threat of data breaches and the increasing importance of privacy by implementing stricter regulations to protect individuals' personal information.
Security and privacy laws, regulations, and compliance
As we look towards 2024, there is a foreseeable trend of more comprehensive privacy regulations and a heightened focus on compliance requirements. Organizations must invest in robust data protection measures, conduct regular audits, and demonstrate compliance with these regulations to avoid legal consequences.
7. Ransomware Attacks
Ransomware attacks have been a persistent threat in recent years, with cybercriminals encrypting victims' data and demanding a ransom for release. Unfortunately, these attacks are expected to continue evolving and becoming more sophisticated in 2024.
What is Ransomware? | IBM
Organizations will need to invest in proactive ransomware defense mechanisms such as regular backups, network segmentation, employee training, and incident response plans to minimize the impact of such attacks.
8. Biometric Authentication
Passwords have long been a weak link in Cybersecurity due to their susceptibility to theft or brute force attacks. Numerous organizations are adopting biometric authentication methods like fingerprint recognition, facial recognition, or iris scanning to address this.
Biometric Authentication Technology and Biometric Data? | Biometric Security
It is projected that by 2024, the use of biometric authentication will become even more widespread, as it offers enhanced security without sacrificing user convenience.
9. Cybersecurity Workforce Shortage
The demand for cybersecurity professionals continues to outpace supply, creating a significant workforce shortage.
The growing reliance on technology and the constantly evolving threat landscape have emphasized the significance of maintaining a resilient cybersecurity workforce.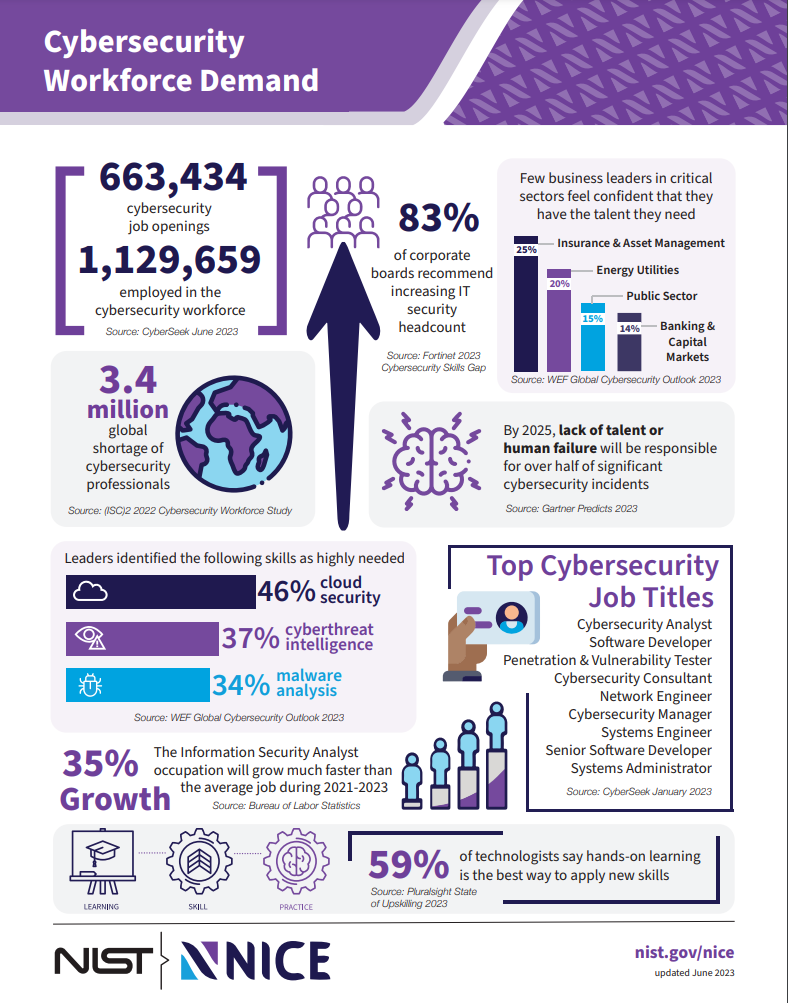
PDF: Cybersecurity Workforce Demand
2024, this shortage is expected to persist or worsen as technology advances and new threats emerge.
- The cybersecurity workforce shortage will decline in 2024, with an increasing demand for skilled professionals.
- The lack of cybersecurity professionals is a global issue, affecting organizations across various industries and sectors.
- According to industry reports, it is estimated that there will be a shortfall of over 3.5 million cybersecurity jobs worldwide by 2024.
- The cybersecurity workforce shortage poses a significant challenge to organizations, increasing the risk of cyber threats and data breaches.
- There is a growing emphasis on promoting cybersecurity education and training programs to address the shortage to attract and develop a new generation of skilled professionals.
Organizations must invest in training programs, partnerships with educational institutions, and automation technologies to address this challenge to augment their workforce.
10. Cyber Insurance
With the growing prevalence and expense of cyber threats, there is a rising interest in cyber insurance as a means to transfer risk.
Many individuals and organizations recognize the importance of having a financial safety net to mitigate the potential damages and liabilities associated with cyber attacks.
By transferring the risk to an insurance provider, policyholders can gain peace of mind knowing they have a backup plan if their systems are compromised.
PDF: CYBERSECURITY FOR Small Business: Cyber Insurance
The year 2024 is expected to rise in organizations opting for cyber insurance policies to effectively handle the potential financial losses resulting from data breaches or cyber-attacks.
Insurers will likely refine their offerings to align with emerging risks and provide tailored coverage that addresses specific cybersecurity needs.
Looking Ahead to 2024
Given the growing sophistication of cyberattacks, it is imperative to safeguard sensitive information and infrastructure proactively.
The rise of artificial intelligence and machine learning will revolutionize cybersecurity defenses and attack techniques, necessitating constant evolution in strategies.
The year 2024 will emphasize the importance of collaboration between industry experts, government agencies, and cybersecurity professionals to establish a robust and secure digital ecosystem, thus minimizing the risks posed by cyber threats.
----
Want to learn about Cybersecurity?
Incyb3r focuses on cybersecurity education and career advice. I started this blog as a project to share my experience taking a cybersecurity master's degree.
I have also been able to help other people interested in the field by sharing my experiences and knowledge.
👉 Subscribe and Join The Chat
The chat is open to participants of all levels, from novice students wanting to explore the world of Cybersecurity.
Participants can also use the free newsletter, which links relevant articles about cyber-related topics and helpful tips for exploring career options in this ever-evolving sector.
----
References
I originally published it on my cybersecurity blog, InCyb3r.