Hacking a Human
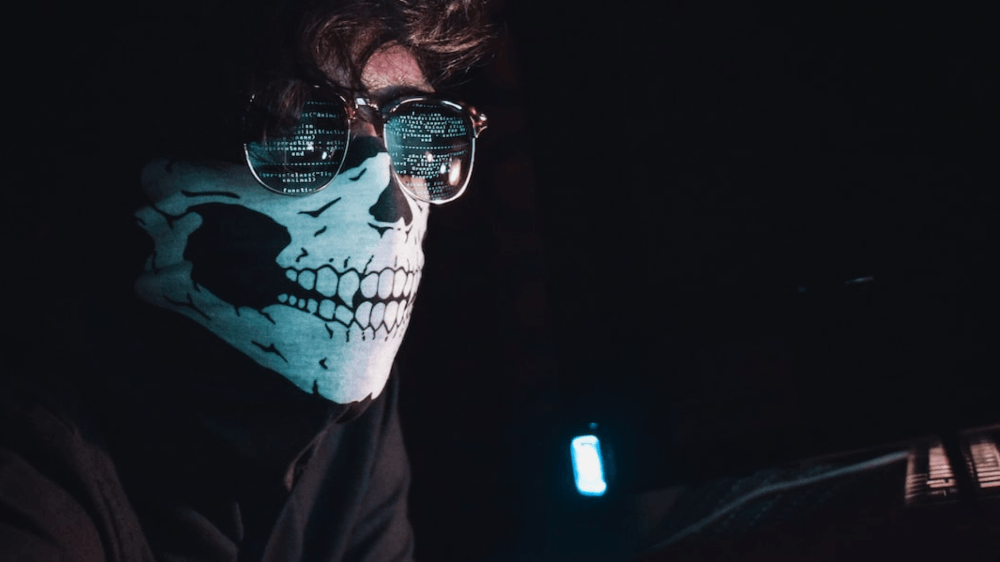
As our world becomes increasingly digitized, so does how criminals can commit crimes.
Social engineering is a type of attack in which hackers use psychological techniques to trick people into giving them sensitive information or access to systems.
The hackers may pose as customer service representatives, IT professionals, or even friends or family members to gain your trust. They may also exploit human emotions like greed or curiosity.
While social engineering can be used for many things, it is most often used to hack human emotions.
Social Engineering Defined
In its simplest form, social engineering is manipulating people into performing actions or divulging confidential information.
A more sophisticated form of social engineering uses psychological manipulation to trick people into making security decisions that are in the attacker’s favor.
What is Social Engineering? | Definition - Kaspersky
Social engineering attacks are usually targeted at specific individuals or groups of people. The attacker will study their target’s behavior and use this information to exploit their trust.
Social Engineering- The art of hacking humans | Prasad Sawant | TEDxElproIntlSchool
Social engineering can access physical locations, such as buildings, offices, computer systems, and networks.
Once an attacker has gained access, they can then use this access to steal sensitive data or plant malware.
The Art of Persuasion
The art of persuasion is a powerful tool that can be used for both good and bad purposes.
Social engineering is a type of persuasion that relies on tricking people into giving up confidential information or doing something against their judgment.
The Art of Persuasion | Psychology Today
While social engineering can be used to take advantage of people, it can also be used for good.
Convincing someone to vote, sign a petition, or donate to a worthy cause are all forms of persuasion that can have a positive impact.
Persuasion is not always easy; sometimes, it takes more than one try to get someone to agree with you.
But if you believe in what you're saying and are persistent, you'll be surprised at how often you can get people to see things your way.
Playing on Human Emotions
Human emotions have long been used as a tool for social engineering. There are many ways to exploit human emotions, but some of the most common are fear, guilt, and greed.
By understanding how people think and feel, scammers and hackers can manipulate them into giving up personal information or doing something against their better judgment.
5 Emotions Used in Social Engineering Attacks [with Examples]
For example, scammers might pretend to be from the IRS and threaten to arrest the person if they don't pay a fake tax bill. Or they might send an email that looks like it's from a friend in need, asking for money to be shipped immediately.
Preying on people's emotions is an easy way to get what you want, but it's also unethical and can have serious consequences.
If you think you're being manipulated this way, staying calm and rational is essential to make the best decision for yourself.
Creating a Sense of Urgency
By creating a sense of urgency, criminals can trick people into revealing information they would otherwise keep private.
One of the most common ways social engineers create a sense of urgency is by pretending to be from a company or organization with which the victim is familiar.
This is what happens when you reply to spam email l TED
They may say that there is an issue with the victim's account or that their personal information has been compromised.
12 Types of Phishing Attacks to Watch Out For | Helixstorm
This can trick victims into giving up their login credentials or other sensitive information.
Another way that social engineers create a sense of urgency is by spoofing email addresses or websites.
They may send an email that looks like it's from a legitimate source, but when the victim clicks on the link, they are taken to a fake website where their personal information can be stolen.
Manipulating Trust
When it comes to social engineering, manipulating trust is critical. Trust is what allows us to believe in others, and it's what allows us to let our guard down.
By manipulating trust, attackers can take advantage of our natural tendencies and exploit them for their gain.
Social Engineering - The Art of Manipulating People - Advantio
To successfully manipulate trust, attackers must first understand how it works. Trust is built on a foundation of shared values and beliefs.
If an attacker can align their goals with the victim's values, they will be more likely to gain their trust. Once the attacker has established trust, they can start exploiting it.
Attackers can use social engineering techniques to manipulate trust for various purposes.
They may use it to gain access to sensitive information or systems or as part of a larger phishing or scamming attack.
Taking Advantage of Human Curiosity
With the vast majority of people now working from home, cybercriminals are taking advantage of human curiosity to target individuals with social engineering attacks.
These attacks exploit the natural human tendency to be curious and click on links or open attachments without thinking twice.
The Power Of Emotions: How Cybercriminals Are Taking Advantage of Psychology
Cybercriminals send phishing emails that look like they’re from a legitimate source, such as a company or government agency.
The email may contain a sense of urgency or fear, prompting the recipient to click on a link or open an attachment without thinking twice.
However, once clicked, the recipient’s computer is infected with malware that can give the attacker access to sensitive information.
Individuals can protect themselves from social engineering attacks by being aware of these tactics and not clicking on links or opening attachments from unknown sources.
Making it Personal
One of the most common ways social engineers exploit people is by impersonating someone they trust.
Scammers often pose as customer service representatives from a well-known company to access someone's personal information.
Impersonation in social engineering - My Security Awareness
They may also send phishing emails that appear to be from a legitimate source to get recipients to click on a malicious link or attachment.
Another way social engineers take advantage of people is by playing on their emotions. For example, scammers may pose as a family member needing money or as a charity collecting donations for a good cause.
Final Thought
Cyber attacks are not limited to machines but can target humans as well. The most vulnerable area of attack is humans, that are more easily tricked into divulging information or performing an action that will allow the attacker access to a system. This is known as social engineering.
The best way to protect against social engineering attacks is to educate yourself and your employees about the dangers and train them to be vigilant.
Organizations should also have policies and procedures to prevent and respond to these attacks.
References
I originally published it on my cybersecurity blog, InCyb3r.