What is Cyber Hygiene?
Photo by Becca Tapert on Unsplash.
Technology is an integral part of our lives, and the effects of human behavior on cyber security cannot be underestimated. Our actions and decisions significantly impact the safety and integrity of our digital environment.
How does human behavior influence cyber security? In this short post, let's highlight the importance of adopting good online hygiene practices.
Cyber Hygiene
Cyber hygiene refers to the practices and measures computers, and other digital devices use to maintain system health and improve online security. These practices are often part of a routine to ensure identity safety and further details that could be stolen or corrupted.
Like personal hygiene, cyber hygiene is regularly conducted to ward off natural deterioration and common threats. Cyber hygiene can cover various activities, from maintaining system and software updates to managing passwords.
A strong cyber hygiene routine can help protect users from identity theft, data breaches, and hardware corruption. It can also help prevent attacks from common malware, such as viruses and ransomware.
Regular backups, setting up firewalls, updating software, using strong, unique passwords, and not opening suspicious emails or links are some of the practices associated with good cyber hygiene.
As you brush your teeth to prevent cavities, you should follow good cyber hygiene to avoid cyber threats.
The Importance of Cyber Hygiene
One of the key ways in which human behavior affects cyber security is through the practice of good online hygiene. By adopting safe browsing habits, individuals can significantly reduce their vulnerability to cyber threats. Let's share here some rules to follow:
- Using Strong Passwords: Creating unique and complex passwords for each online account is crucial. Avoid using easily guessable passwords such as your name or birthdate. Instead, combine upper and lower case letters, numbers, and special characters.
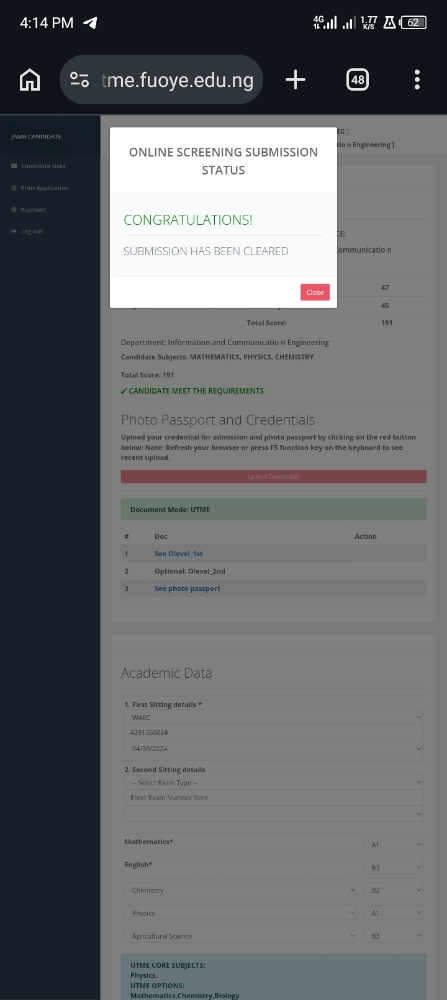
How to Use Passwords and Be Safer Online: Nick Berry at TEDxSeattle
- Being Cautious of Suspicious Emails and Websites: Phishing attacks are a standard method cybercriminals use to steal sensitive information. Always verify the sender’s email address and avoid clicking on suspicious links or downloading files from untrusted sources.
- Regularly Updating Software and Antivirus Programs: Keeping your software and antivirus programs current is essential. Updates often include patches for security vulnerabilities, so staying current helps protect against emerging threats.
Mindful Sharing of Information
Being mindful of the information we share online is another crucial aspect of maintaining cyber security. Oversharing personal details can lead to identity theft and data breaches. Follow here some best practices to consider:
- Limiting Personal Information: Be cautious when sharing personal information on social media or other platforms. Unless necessary, avoid posting details such as your full name, address, phone number, or financial information.
- Understanding Privacy Settings: Familiarize yourself with the privacy settings of your platforms. Adjust the settings to limit the visibility of your profile and personal information to only trusted individuals.
Cyber Immunity: Raising Cyber Security Awareness | Minh Hieu Ngo
- Being Aware of Consequences: Consider the potential consequences of your actions before sharing information online. Once something is posted, removing it can be challenging, so think twice before sharing anything that could compromise your privacy or security.
Risks of Poor Human Behavior
Poor human behavior can create substantial risks to cyber security. Negligence and carelessness can provide cybercriminals with easy access to sensitive data. Awareness of common cyber threats is essential to minimize these risks:
- Clicking on Unknown Links: Clicking on unknown links, especially emails or messages from unknown sources, can lead to malware infections or phishing attacks. Always verify the legitimacy of the link before clicking.
- Downloading Files from Untrusted Sources: Downloading files from untrusted sources can introduce malware onto your device. Stick to reputable websites and only download files from trusted sources.
- Lack of Awareness about Common Cyber Threats: Phishing scams, social engineering tactics, and other cyber threats constantly evolve. Staying informed and educating yourself about these threats is crucial to recognize and avoid falling victim to them.
The Impact of Offline Behavior
Our offline behavior also has an impact on cyber security due to our increasing reliance on technology and interconnected devices:
- Weak Passwords: Weak or easily guessable passwords can compromise individual accounts and entire networks. Creating strong passwords and avoiding using the same password across multiple accounts is essential.
- Unsecured Physical Devices: Failing to secure physical devices, such as leaving smartphones unattended or not properly disposing of old computers, can lead to unauthorized access and potential data breaches. Always lock your appliances when not in use and ensure proper disposal methods for electronic devices.
Final Thought
Human behavior is crucial in determining cyber security in our digital world. By practicing good cyber hygiene, staying informed about emerging threats, and being mindful of our online and offline actions, we can create a safer and more secure cyber environment for everyone.
We must remember that our efforts collectively have the power to impact cyber security significantly. Let’s prioritize responsible behavior and ensure a safer digital future for all.
----
Looking to Learn about Cybersecurity?
Incyb3r focuses on cybersecurity education and career advice. I started this blog as a project to share my experience taking a cybersecurity master's degree.
I have also been able to help other people interested in the field by sharing my experiences and knowledge.
👉 Subscribe and Join The Chat
The chat is open to participants of all levels, from novice students wanting to explore the world of cybersecurity.
Participants can also use the free newsletter, which links relevant articles about cyber-related topics and helpful tips for exploring career options in this ever-evolving sector.
----
References
I originally published it on my cybersecurity blog, InCyb3r.