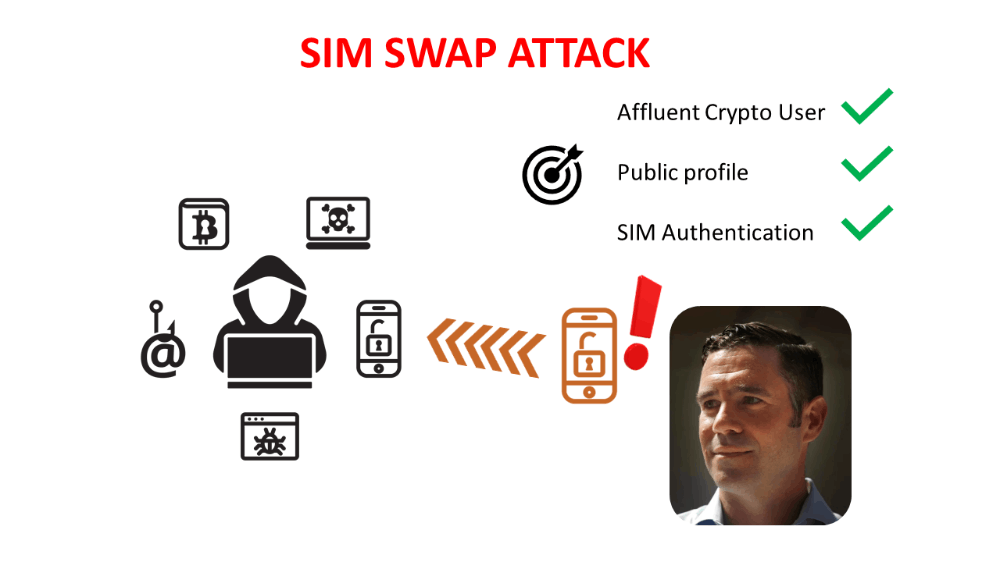
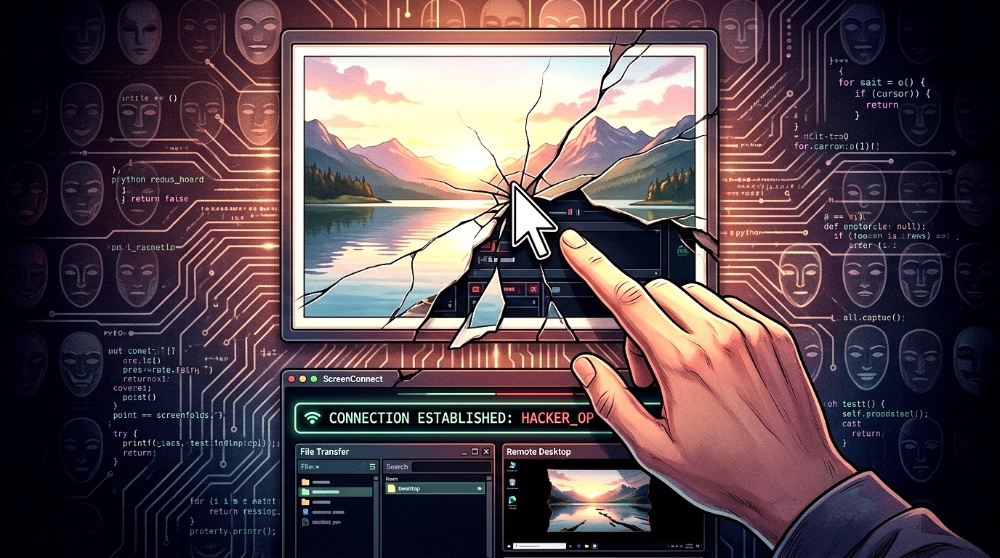
Blockchain Capital Bart Stephens SIM SWAP Hack - Could Have Been Prevented?
Bart Stephens, cofounder and managing partner of crypto fund Blockchain Capital was the victim of a SIM SWAP hack.
And, the consequences for him are as follows:
- 6.4 million US dollars worth of Bitcoin, Ether, and other cryptocurrencies were taken from his wallet(s)
- He has become news, about how a partner from a well-known crypto fund has been hacked.
None of those are good for him.

What Did It Happen?
Mr. Stephens states that a hacker used personal information publicly available online and also personal information available in the dark web, to successfully perform a SIM SWAP hack on him.
After the hacker was able to port Mr.Stephen's cell number from his SIM card to a SIM card that the hacker controlled, the hacker was able to use this access to reset financial account passwords and also pass two-factor authentication (2FA) tests.
With access to Mr. Stephen's crypto assets, the hacker was able to move them to a crypto wallet(s) under the hacker's control.
Fortunately, not all his assets were lost, because a substantial amount of Ethereum was stored in a custodial cold wallet and when the hacker tried to access the assets this triggered a notification that alerted Mr.Stephens.
Could the SIM SWAP Have Been Prevented?
Most probably yes. But not 100% certainly.
Mr.Stephens is a public figure and it is known that he owns considerable amounts of cryptocurrencies.
As a known crypto owner, that makes him a desirable target for organized criminals.
And as a public figure, a lot of his personal information can be found on the net.
Hackers and scammers will target those people who they know they have significant amounts of crypto assets. Time is money, even for hackers and scammers, so they look for profitable targets.
Knowing this, Mr.Stephens could have contacted his cell phone provider and instructed them to be alert and to shield his accounts against SIM SWAPS.
Such as adding a PIN or password to his user account, which is requested every time an account change is solicited.
How to Minimize the Consequences of a SIM SWAP
If the hackers have enough knowledge and resources, they can still push forward a SIM SWAP.
You may take measures, but always there is a weak link somewhere and if you are a profitable target the hackers will pour enough resources to exploit that weak link.
So, having mobile phone message notifications as Two-Factor Authentication (2FA) is a very bad approach to digital security.
But, having mobile phone message notifications as Multi-Factor Authentication (MFA) is acceptable.
The consequence of being the victim of a SIM swap could have been prevented by using MFA or a more secure type of 2FA.
But given the extent of his crypto portfolio, the best approach would have been to use both a secure 2FA app and hardware token as MFA.
This way, even in the case of a SIM SWAP, his crypto assets could have been inaccessible to the hackers, without first having to crack the additional authentication method.
Should You Shield Yourself From SIM SWAP Attacks?
The answer is Yes.
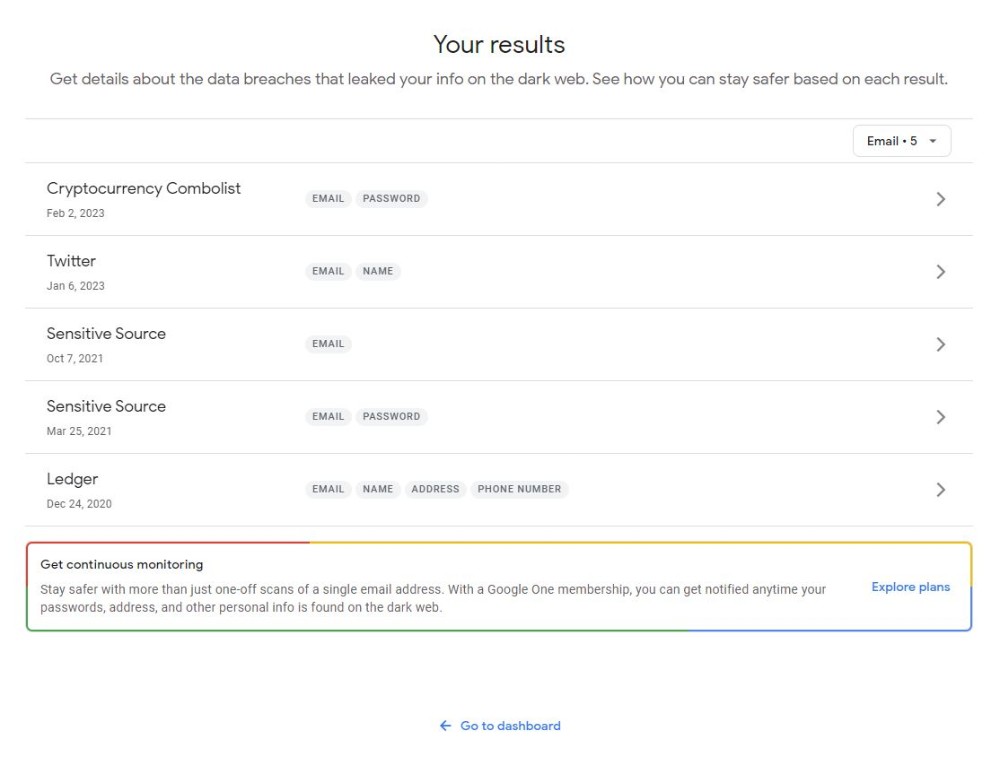
You may not be a crypto millionaire or a public figure but you never know how much of your personal information has been available to people with bad intentions.
Your data could be on the dark web making you an easier target. If any of your data has been leaked and has any relation with crypto, that may ring some bells, and maybe some hacker or scanner decides to give it a try.
If any of your data has been leaked and has any relation with crypto, that may ring some bells, and maybe some hacker or scanner decides to give it a try.
Why take risks? Maybe it is time to have a chat with your SIM service provider or make sure that SIM message authentication is not used as 2FA for any of your personal or financial accounts.
__________________________________________________________________________________________________
Before we conclude this article, please think twice before commenting on Mr. Stephens's situation.
Many people fall victim to hacks and scams, not for negligence or lack of knowledge, but for lack of awareness.
Let's be comprehensive and work towards bringing digital and crypto safety awareness to as many people as possible to prevent hackers and scammers from taking advantage.
At Crypto Safety First we hope that learning from real stories brings awareness that hacks and scams do not happen to other people, or in movies. The more aware we are, the safer we will be.
__________________________________________________________________________________________________
Congratulations on completing this 5-minute digital safety power-up.
We hope this short article has helped increase your digital safety knowledge and awareness, and the 5 minutes read was worth the time. If you have additional time, consider digging deeper and learning about Two-Factor Authentication (2FA) types. (Follow the link to find a handy quiz to test your 2FA knowledge).
If you have additional time, consider digging deeper and learning about Two-Factor Authentication (2FA) types. (Follow the link to find a handy quiz to test your 2FA knowledge).
__________________________________________________________________________________________________
Article originally published at: https://www.publish0x.com/@Crypto-Safety-First