Software wallet and risk
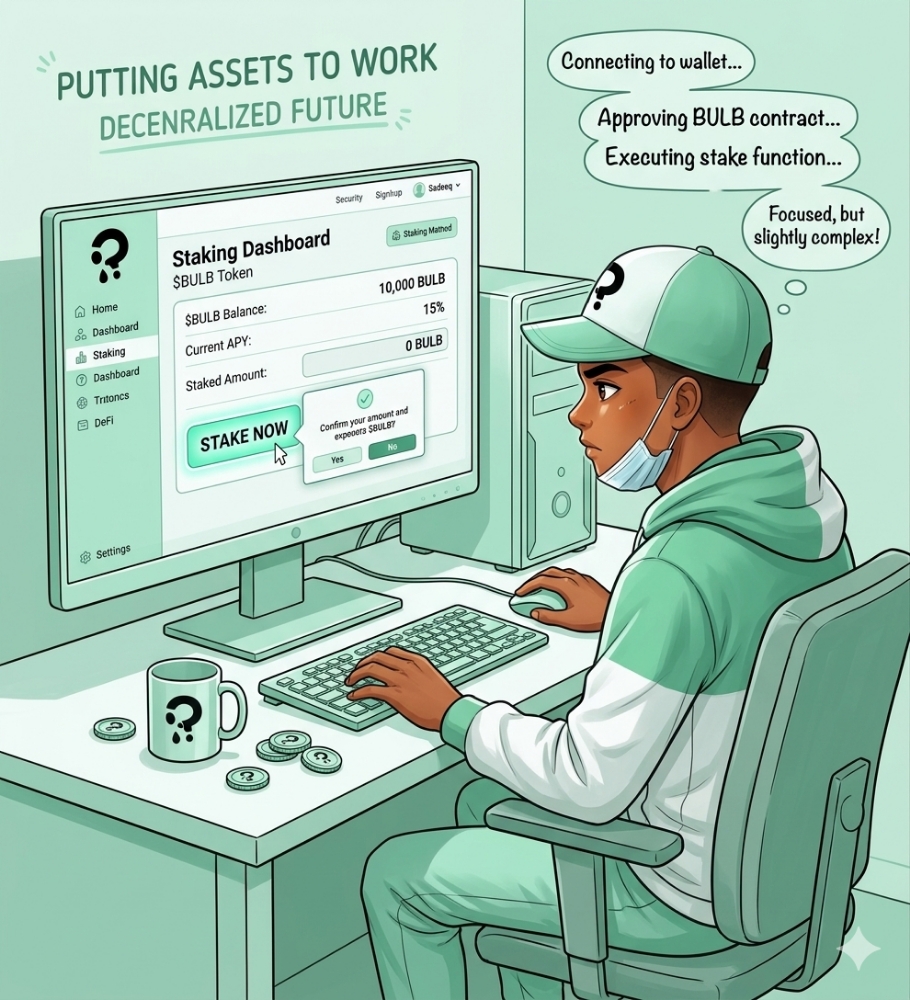
A software crypto wallet is a digital wallet application that allows users to store, send, and receive cryptocurrencies. Unlike traditional physical wallets that hold cash and cards, a crypto wallet stores cryptographic keys, which are used to access and manage the ownership of cryptocurrency funds on a blockchain.
There are different types of software crypto wallets, including:
1. Desktop Wallets: These are applications installed on a computer and can be used to store and manage cryptocurrency keys. Examples include Electrum (for Bitcoin) and Exodus.
2. Mobile Wallets: These are wallet applications designed for smartphones and tablets, making it convenient for users to manage their cryptocurrencies on the go. Examples include Trust Wallet and MyEtherWallet.
3. Web Wallets: These wallets operate through a web browser and are accessible from any device with internet connectivity. Users need to be cautious with web wallets as they involve an element of trust in the service provider. Examples include Coinbase and Blockchain.info.
4. Hardware Wallets (with Software Interface): While hardware wallets are physical devices that store cryptocurrency keys offline for enhanced security, they often come with a software interface that allows users to interact with the wallet and perform transactions. Examples include Ledger and Trezor.
5. Online Wallets: These are wallets hosted on the cloud, and users can access them through a web browser. Security concerns are higher with online wallets, as users are dependent on the security measures implemented by the service provider. Examples include exchanges like Binance and Kraken, which offer wallet services.
It's important to note that crypto wallets store private keys, which are crucial for accessing and controlling the associated funds. Users should prioritize security measures such as using strong passwords, enabling two-factor authentication, and keeping backup copies of their recovery phrases or private keys. Additionally, users should be cautious and only use reputable wallet services to minimize the risk of unauthorized access or loss of funds.
Software crypto wallets, also known as hot wallets, are digital wallets that run on software applications, devices, or online platforms. These wallets offer several advantages, making them popular choices for users in the cryptocurrency space. Here are some of the key advantages of software crypto wallets:
1. Convenience:
• Software wallets are easily accessible on various devices such as computers, smartphones, and tablets. Users can manage their crypto assets conveniently from anywhere with an internet connection.
2. User-Friendly Interfaces:
• Many software wallets have user-friendly interfaces, making them accessible to both beginners and experienced users. The intuitive design often simplifies the process of sending, receiving, and managing cryptocurrencies.
3. Cost-Effective:
• Software wallets are generally free to download and use, making them a cost-effective option for individuals who want to manage their crypto assets without incurring additional expenses.
4. Quick Setup:
• Setting up a software wallet is typically a quick and straightforward process. Users can create a wallet, generate a recovery seed, and start using it within a short period.
5. Regular Updates:
• Developers often release updates for software wallets, which may include security enhancements, bug fixes, and new features. Users can easily update their wallets to benefit from the latest improvements.
6. Integration with Exchanges:
• Many software wallets are compatible with cryptocurrency exchanges, allowing users to seamlessly transfer funds between their wallet and exchange accounts.
7. Multi-Currency Support:
• Some software wallets support multiple cryptocurrencies, providing users with flexibility and the ability to manage a diverse portfolio of digital assets in a single wallet.
8. Backup and Recovery Options:
• Software wallets typically include backup and recovery features, such as mnemonic phrases or seed words. Users can use these to restore their wallet and access their funds in case of device loss or failure.
9. Private Key Control:
• Users have direct control over their private keys in software wallets. This control enhances security by reducing the reliance on third parties.
10. Customization:
• Some software wallets offer customization options, allowing users to choose security settings, transaction fees, and other preferences according to their needs.
11. Security Features:
• While hot wallets are connected to the internet, many software wallets implement robust security features, such as encryption, password protection, and two-factor authentication (2FA), to help safeguard users' funds.
It's essential for users to research and choose reputable software wallets and take appropriate security measures, such as keeping their software up to date, using strong passwords, and securely storing backup phrases.
Software crypto wallets, also known as hot wallets, come with certain disadvantages that users should be aware of. Here are some common disadvantages:
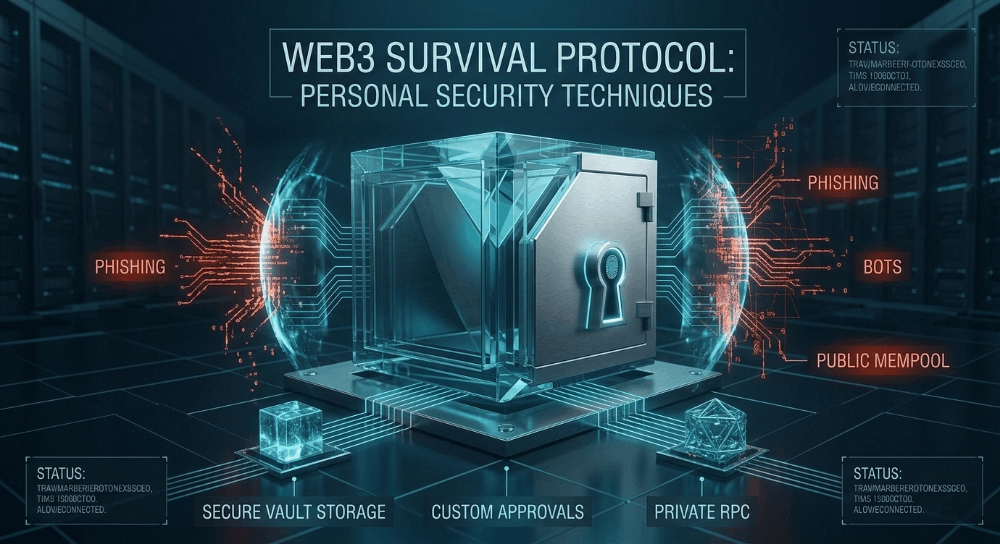
1. Security Risks:
• Online Vulnerabilities: Software wallets are connected to the internet, making them susceptible to online threats such as hacking, malware, and phishing attacks.
• Private Key Exposure: If your device is compromised or infected with malware, there is a risk that your private key, which is crucial for accessing your funds, could be exposed.
2. Dependency on Devices:
• Device Reliance: Software wallets depend on the security of the device they are installed on. If the device is lost, damaged, or compromised, it may lead to a loss of access to the wallet and funds.
3. User Errors:
• Human Mistakes: Users may make mistakes such as forgetting passwords, losing access credentials, or falling victim to social engineering attacks, leading to potential loss of funds.
4. Internet Connectivity Issues:
• Access Dependency: Software wallets require an internet connection to perform transactions. If there are issues with internet connectivity, users may face difficulties in accessing their funds or executing transactions.
5. Centralized Points of Failure:
• Server Downtime: Some software wallets rely on centralized servers, and if these servers experience downtime or face technical issues, it can impact the functionality and accessibility of the wallet.
6. Limited Anonymity:
• Identity Verification: Some software wallets may require users to go through identity verification processes, compromising a degree of anonymity that is often associated with cryptocurrencies.
7. Development Issues:
• Software Bugs: Like any software, wallets may have bugs or vulnerabilities that could be exploited. Regular updates and patches are essential to address these issues, but they also require user diligence in keeping their software up to date.
8. Lack of Physical Tangibility:
• No Physical Backup: Unlike hardware wallets, which can be physically stored and kept offline, software wallets lack a tangible backup option. This makes them more susceptible to data loss in case of device failure.
It's important for users to weigh these disadvantages against the convenience and accessibility offered by software wallets and consider their individual security needs and risk tolerance before choosing a wallet solution