Web3 Security: Protecting Against Hackers and Fraudsters
Web3, favored by many, is considered vulnerable to hackers and fraudsters despite its security features.
Fraudulent activities, large gains, investments or special advantages occurring in this area are described as investment fraud by the US Federal Trade Commission (FTC).
There is a report on the subject published by the Federal Trade Commission in June 2022. According to the report, more than $1 billion worth of cryptocurrency fraud activities have occurred since 2021.
The FTC report includes the following statements regarding this issue:
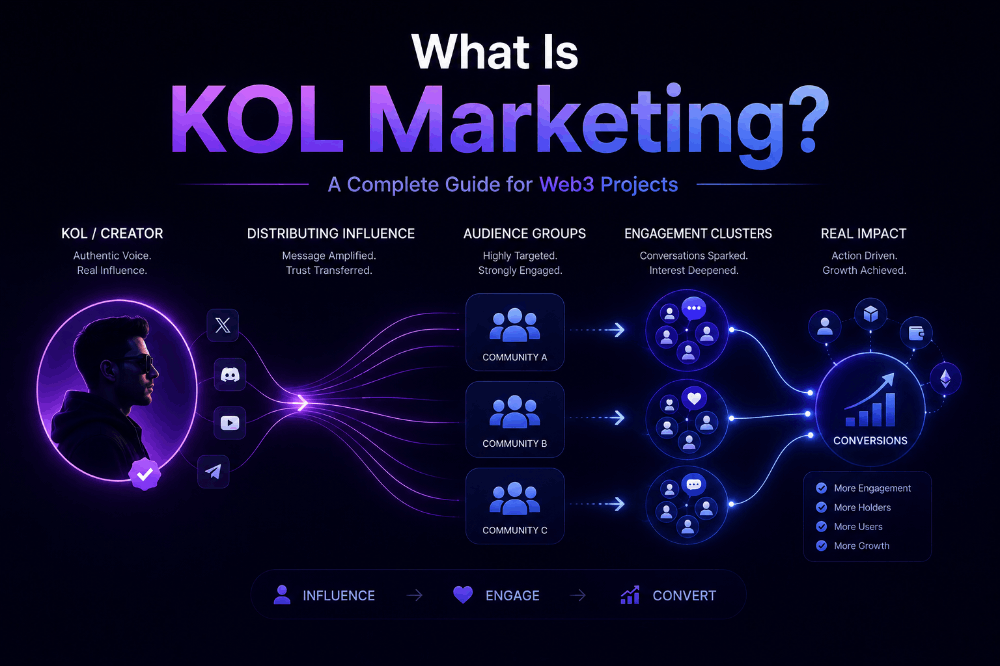
“Almost half of people who reported losing their cryptocurrency to a scam since 2021 said it started with an ad, post or message on the social media platform.”
NFTs are the Target of Attackers
Although fraudulent activities are aimed at cryptocurrencies, NFTs have also become an increasingly popular target for fraudsters. It seems that some details on this subject are included in a report published by Web3 cyber security firm TRM labs .
Attackers are specifically targeting high-value NFT collections. For example, approved projects such as Bored Ape Yacht Club (BAYC), one of the popular collections, are seen as a worthy goal. In fact, in April 2022, the BAYC Instagram account was attacked by scammers who redirected users to a site to steal cryptocurrencies and NFTs from their Ethereum wallets. After this attempt, 91 NFTs with a total value of over 2.8 million dollars were stolen. In yet another attack, NFTs worth 200 ETH were stolen from users through a referral via Discord.
Of course, since the target of fraudsters is NFTs with high value, the wealthy audience who own them was also affected by this situation.
Security Companies Monitoring
These increasing fraudulent activities in the Web3 area have mobilized many security companies. Making a statement on this issue, Luis Lubeck, a security engineer at cyber security firm Halborn, stated that phishing attacks are still the first attack vector. In his statement, Lubeck says that users should be aware of wallet credentials, cloned links, fake projects and fake websites.
According to Lubeck, phishing scams start with social engineering. In other words, the attacker sends messages to the targeted audience/person stating that they have the opportunity to get an early token or that their money will be increased 100 times. Then, they send them various redirects with fake links. Some users who see the attacker's message as an opportunity and do not want to miss it may also fall into this trap. So he kind of gets caught up in FOMO.
Types of Cyber Attacks
There are many types of attacks occurring in the digital space. Although there is no single list of the types of attacks that negatively affect users, there are some known methods. Now let's examine these in a few items.
1- Phishing Attacks : Phishing attacks are one of the most well-known and most widely used types of cyber attacks. In this attack method, users generally receive notifications in the form of e-mail. These messages, which appear to come from a known brand or platform, direct users to other sites.
When users click on this link and connect to the wallet, the system is activated. Thus, the attacker can easily steal cryptocurrencies or NFTs in the user's browser-based wallet. The important point here is that users need to make the necessary checks before clicking on these links immediately.
2- Malware : This type of attack is one of the commonly used methods. Malware takes control of users' systems by transferring all harmful programs or codes to them. The method used is phishing e-mails, texts and messages sent to the user.
3- Compromised Websites : In this type of attack, users think that they are entering a legitimate website, but actually enter the site that has been taken over by criminals. When users click on a link, image or file on these websites, they download malware to their devices.
4- URL Spoofing: In this method, fake websites are created by cloning legitimate websites. Users should unlink these compromised websites and refrain from taking any action on the site. Also known as URL Phishing, these sites can collect users' names, passwords, credit cards, cryptocurrencies, and other personal information.
5- Fake Browser Extensions: As the name suggests, this attack method directs cryptocurrency users to enter their credentials or keys into an extension that allows cybercriminals to access data. Fake browser extensions are used for this purpose.
These attacks often aim to access, steal and destroy sensitive information or, as happened to Green, data in the wallet.
So How Do We Protect ourselves from Attacks?
There are several methods to protect against all these attacks. In fact, the most important thing to do here is to be a little careful. Lubeck, a security engineer, says the best way to protect users from phishing attacks is to never respond to an email, SMS, Telegram link or WhatsApp message from an unknown person, company or account.
You should not enter your identity information or personal information when using WiFi connections located or shared in public areas.
How Should We Store Our Cryptocurrencies and NFTs?
There are several methods to protect the cryptocurrencies and NFTs we own. Using an external hardware or wallet to store digital assets. These devices, known as “ cold wallets ” in the cryptocurrency market , are active only when users want to use them.
In other words, your assets are safe since there is no internet access. Although currently widely used browser-based wallets like MetaMask are convenient and fast, remember that anything connected to the internet has the potential to be hacked.
If you use a mobile, browser or desktop wallet, also known as a “ hot wallet ”, download them from official platforms such as the Google Play Store, Apple's App Store or verified websites.
Never download from links sent via text or email. Of course, after performing these operations, that is, after contacting a site, be sure to disconnect the wallet from the website.
Do not share your private keys, recovery words and passwords with anyone, especially for hot wallets. Because lately, some attackers have been asking for user information to access their information. As it is known, the airdrop distribution frenzy of new projects has started recently.
Therefore, only connect your wallets to sites that are safe and that you have researched. If someone asks you to share this information to participate in any investment, airdrop or cryptocurrency transaction, rest assured that this is most likely a fraudulent activity.
Ultimately, only invest in projects you understand and trust. If you are unsure of its safety or accuracy, you should do further research. To continue keeping your assets safe, it will be beneficial for you to be careful and do more research.