The Complete Blueprint: How Cryptocurrency is Created, Mined, and Distributed via Airdrops
The Complete Blueprint: How Cryptocurrency is Created, Mined, and Distributed via Airdrops
Introduction: The Digital Ledger Revolution
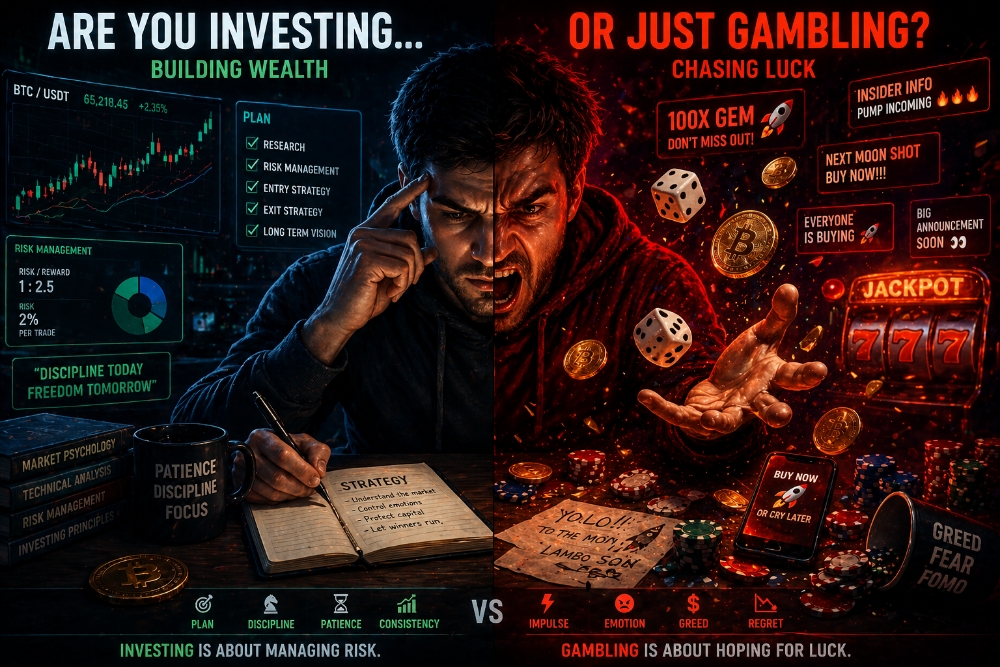
The question that echoes most frequently in the corridors of the nascent Web3 economy is both simple and profound: "Where does cryptocurrency actually come from?" To the uninitiated, digital assets appear to materialize ex nihilo (out of nothing), fluctuating wildly in value with no apparent anchor to the physical world.
This perception is, fundamentally, a misunderstanding of how digital value is secured and distributed. Cryptocurrency is not "printed" like traditional fiat currency; it is generated by code, secured by mathematics, and distributed through strategic community building and raw computational proof.
This comprehensive blueprint is designed for the modern reader—whether an investor, a developer, or a curious skeptic—to deconstruct the primary mechanisms of digital genesis. We will analyze the brute-force security of Proof of Work (PoW) Mining, the decentralized scaling power of Airdrops, and the regulatory and technical reasons why these systems have become the two main pillars of the crypto economy in 2026.
This is the definitive guide to understanding how value is built in the digital age.
Part 1: The Industrial Revolution of Code: Proof of Work (PoW) Mining
To understand the genesis of any Proof of Work cryptocurrency, you must first understand the problem it solves: The "Double-Spending" problem in a decentralized network. Without a central bank, how can the network ensure User A doesn't send the same 1 BTC to both User B and User C at the same time?
The solution, proposed by Satoshi Nakamoto, was Bitcoin Mining. Mining is the original, rugged, and energy-intensive method of creating a digital asset from scratch. It is the core mechanism that forces the network to converge on a single, immutable truth.
The "creation" of the coin is not the primary function; rather, the creation is the payment given to those who secure the network.
I. The Physical Infrastructure of Digital Security
When we discuss "mining" in the context of Bitcoin or other PoW chains, we are describing the conversion of raw electricity and powerful hardware into network consensus. It is a mathematical arms race.
Here is a 10-point, step-by-step blueprint of how the hardware-intensive mining process actually works:
- 1. ASIC and GPU Domination: Miners use highly specialized hardware. For Bitcoin, it is ASICs (Application-Specific Integrated Circuits), machines designed for the singular purpose of solving one specific cryptographic puzzle. For other PoW chains, high-end GPUs (Graphics Processing Units) are used.
- 2. The Mathematical Puzzle (Hashing): The blockchain network generates an incredibly complex math problem. This is not a standard equation. It is a "Hash," a unique, 64-character alphanumeric string. In Bitcoin's case, it uses the SHA-256 algorithm.
- 3. Finding the 'Nonce': The challenge for the miner is this: The network's code provides a "target" value (a specific starting sequence for the Hash). Miners must find a random number (the nonce) which, when added to the data from all the pending transactions, produces a final Hash that is smaller than or equal to the target value.
- 4. Computational Brute Force: There is no formula for finding the nonce. The hardware must guess trillions of random nonces per second. This metric is called Hash Rate. A higher hash rate means more guessing power and a higher statistical probability of winning the lottery.
- 5. The Global Competition: Miners around the world are racing simultaneously against the same puzzle. The difficulty of this puzzle automatically adjusts (roughly every two weeks) to ensure that, on average, a block is solved every 10 minutes, regardless of how many miners are competing.
- 6. Block Verification and Consensus: When a miner finally finds the correct nonce, they "broadcast" the solution to the entire network. All other miners immediately stop, verify the solution (this verification is instant and free), and accept that the winner has successfully secured the block.
- 7. Appending the Chain: The winner writes the newest batch of verified transactions (the "Block") to the blockchain. This block is digitally linked to the previous one via its Hash, forming an unbreakable, chronological, public ledger. This is the Proof of Work.
- 8. The Transaction Fees Reward: As a first reward for their service, the winning miner is paid all of the individual transaction fees (the "satoshis-per-byte" cost) attached to every transaction included in that specific block.
- 9. The Block Reward (Creation): The second, and most substantial, reward is the Block Reward. This is the creation of brand-new cryptocurrency that never existed before. The network's code allows the winner to create a special transaction—the Coinbase Transaction—which awards them a predetermined amount of the asset (e.g., 3.125 BTC as of 2026). This is the only way new coins are created in a PoW system.
- 10. The Network's Janitor and Guard: Miners are the network’s self-interested protectors. They are financially motivated to behave honestly and use their massive computational power to secure the ledger, ensuring that the double-spend problem is solved.
Part 2: Moving the Ledger: The Security Imperative
Miners are often criticized for their environmental footprint, but their function is non-negotiable for decentralized security. We can break down their utility into three core functions:
- Immense Network Security: The "brute force" nature of PoW means that in order to "attack" or alter the historical ledger of Bitcoin, an adversary would need to control more than 51% of the entire global hash rate. In 2026, the cost in electricity and ASIC hardware required to achieve this is functionally impossible, making the network practically unbreakable.
- Decentralized Monetary Policy: Mining provides a rules-based, predictable inflationary schedule that is not controlled by a central board. Everyone knows the exact rate at which BTC is being created and the precise date of the next "Halving" (when the Block Reward is permanently cut in half). This transparency creates a level of monetary predictability that no fiat central bank can match.
- Self-Custody and Censorship Resistance: Because the system is secured by mathematics rather than trusted individuals, no government or corporation can "freeze" a transaction signed with your private key and validated by miners. As long as you follow the network rules, your transaction will be included.
Part 3: The Scaling Power of Web3: Digital Airdrops
If mining builds the unbreakable infrastructure, Airdrops build the bustling metropolis on top of it. They are two sides of the same digital genesis coin. Mining is used to build security; Airdrops are used to build scale, utility, and community.
In the highly competitive Web3 economy of 2026, where attention is the single scarcest resource, Airdrops have evolved from a simple gimmick into the single most potent tool in the digital marketing arsenal. Instead of users competing to generate coins (brute force), project founders send existing or new tokens directly to users' wallets for free (community force).
I. The Taxonomy of Modern Airdrops
Just as there are different types of computational hardware, there are different types of Airdrop campaigns. We can categorize them into five main archetypes that are active in 2026:
- 1. Holder Airdrops (The Snapshot Model): This is the classic, passive method. A project will announce that it is taking a "Snapshot" of a specific blockchain at a specific date and time. Anyone holding a particular token (e.g., holding 10 SOL on the Solana chain) at that exact moment will automatically be "airdropped" the new token proportional to their holdings. This creates value for long-term "HODLers."
- 2. Retroactive Rewards (The Loyalty Model): This is the most famous type of modern airdrop (pioneered by DeFi giants like Uniswap and Arbitrum). Projects launch a product without a native token. They let thousands of people use the beta platform for months or years. Then, they announce that all early users who interacted with the platform before a certain date (the snapshot) are entitled to claim a significant allocation of the newly launched governance token. This rewards those who used the protocol, not just those who held a token.
- 3. Task-Based or Bounties (The Community Model): This is the most structured form of airdrop, designed to generate social and technical engagement. Projects will ask users to perform simple digital tasks, such as following an official X/Twitter account, joining a Telegram group, inviting friends to a Discord, or interacting with a new dApp (e.g., "Post one article per day on BulbApp"). By performing these verifiable tasks, you are added to a "Whitelist" and will receive tokens shortly after.
- 4. Node Operator Incentives (The Infrastructure Model): To decentralize the data layer, projects need people to run specialized server software called "Nodes." To incentivize this costly and technical work, projects often announce that anyone running a node on their "Testnet" for a specific duration will be rewarded with a massive "Retroactive Airdrop" once the "Mainnet" goes live.
- 5. Decentralization and "Vibe" Airdrops (The Engagement Model): Sometimes, projects just want to quickly distribute their tokens so the community feels a sense of joint ownership. They might airdrop tokens to any wallet that has voted on a major governance proposal in a related ecosystem, or to wallets that hold highly active "Community NFTs," ensuring that the new token is owned by active, engaged participants rather than passive investors.
Part 4: The Strategic 'Why': Value Creation, Not Handouts
It is a common mistake to view airdrops as just "free money." To project founders, an airdrop campaign is a sophisticated strategic play designed to achieve four critical structural goals for a decentralized protocol:
- 1. Immediate, Radical Decentralization: A network controlled by ten wealthy VCs is vulnerable. A network where 500,000 different people hold tokens via an airdrop is resilient. By spreading the tokens far and wide, project founders ensure that a vast, global community has a vested interest in the token’s success.
- 2. Massive Stress Testing: When a major airdrop is announced, thousands of users rush to a platform at the exact same second to check their eligibility and claim their tokens. This serves as a forced, massive, real-world stress test for the dApp, the underlying blockchain, and the user-interface. Projects often find and fix critical bugs after an airdrop claim.
- 3. Regulatory Compliance: Selling tokens directly to the public through an ICO (Initial Coin Offering) can attract extreme regulatory penalties, as these sales are often classified as unregulated securities offerings. Giving tokens away for free (as an airdrop) is much harder to classify as a security under the laws of many jurisdictions, as the "investment of money" element of the definition is absent.
- 4. Community and "Hype" (The Attention Economy): Airdrops generate massive, organic hype. They turn ordinary users into evangelists. If you receive an unexpected $500 in tokens, you are likely to talk about that project on social media, follow their updates, and tell your developer friends. A well-executed airdrop generates far more goodwill and authentic attention than a multimillion-dollar ad campaign.
Part 5: Synthesis: The Two Faces of Genesis
We must stop viewing mining and airdrops as conflicting systems. The digital economy requires both methods to function, but at different life-stages of a network.
Mining is the brute-force secure foundation—it is the bedrock on which trust is built in systems that cannot tolerate single points of failure, like the Bitcoin network. It creates absolute network immutable truth through mathematical proof.
Airdrops are the agile, high-trust application layer built on top of secure chains. They are used to build communities, incentivize specific user behavior (like using a new DeFi dApp or posting on a social crypto site), and achieve decentralization in days or weeks rather than decades.
II. The User Comparison Blueprint
To help the reader decide which method fits their strategy, we can use a direct comparison of the two systems:
- Capital Requirement: Mining is Extremely High. You need to buy ASIC hardware, pay global energy bills, and maintain cooling infrastructure. Airdrops are Very Low to Free. They usually only require your Time (performing tasks), Engagement, and sometimes very small "Gas" transaction fees to claim the tokens.
- Technical Skill: Mining is High. You need to understand hash rates, difficulty adjustments, hardware management, and cooling systems. Airdrops are Low. You need basic Web3 knowledge, like how to use a standard browser wallet (e.g., Trust Wallet or Phantom Wallet) to sign transactions.
- Risk vs. Reward: Mining is High Risk, Long-Term Reward. Your hardware might become obsolete, the difficulty might spike, or the coin's price might drop below your operational cost. Airdrops are Low Risk, Potential Immediate Reward. Your worst-case scenario is spending an hour performing tasks for a token that never launches. Your best-case is spending one hour to receive hundreds or thousands of dollars in "free" tokens.
- Platform Utility: Mining is designed for Network Security. It ensures the basic integrity of the immutable ledger. Airdrops are designed for Protocol Adoption, Decentralization, and Community Building.
Part 6: Conclusion: The Definitive Digital Blueprint
We have now deconstructed the two primary pillars of cryptocurrency creation in 2026. The next time you hear a new token is being launched or a new dApp is being scaled, you can apply this definitive blueprint to analyze its genesis:
- Is it secured through raw computational power? If so, look for its Proof of Work (PoW) Mining infrastructure, its hash rate, and its scheduled inflation. This is the bedrock of network immutable truth.
- Is it scaling through community activity? If so, look for its Airdrop distribution model. Was it a proactive reward? A task-based bounty? A snapshot-holder event? This is the social engine of network adoption.
The digital age has changed the way we build value. We no longer "print" money; we generate it through math and distribute it through code and community. Understanding both the hardware-intensive security of mining and the agile community-driven power of airdrops is the key to mastering the Web3 economy.
Join the Discussion: The algorithm on this platform heavily rewards engagement. Let’s trigger the debate: Are you Team Miner (capital and hardware) or Team Airdrop Hunter (time and engagement)? Which genesis method do you think is more powerful for creating long-term value in 2026? Let me know your strategy in the comments below!
















![Decoding ct[Asset] Logic and Locking DeFi Legos with Composable Credentials](https://cdn.bulbapp.io/frontend/images/4d8039f6-9ebe-4164-870f-10fad439e6bc/1)