Ethical Hacking in Blockchain Security
Weaknesses of blockchain
Security is the cornerstone of distributed ledger technology. However, the relative immaturity of blockchain technology and the resulting security vulnerabilities have led to widespread losses of user funds across multiple projects, among other reasons. Injection attack vectors target not only the client side of distributed applications (often cross-site scripting attacks in Block Explorer), but also servers, databases, and smart contracts. As such, attackers often exploit front-end vulnerabilities to evade complex security his infrastructure. Second, blockchain immutability complicates opportunities for improving security in the post-mainnet stage, as data cannot be changed without the consent of the majority of network nodes. Additionally, most blockchains are public, so anyone can download and store a complete copy of the ledger contents.
Major blockchain vulnerabilities
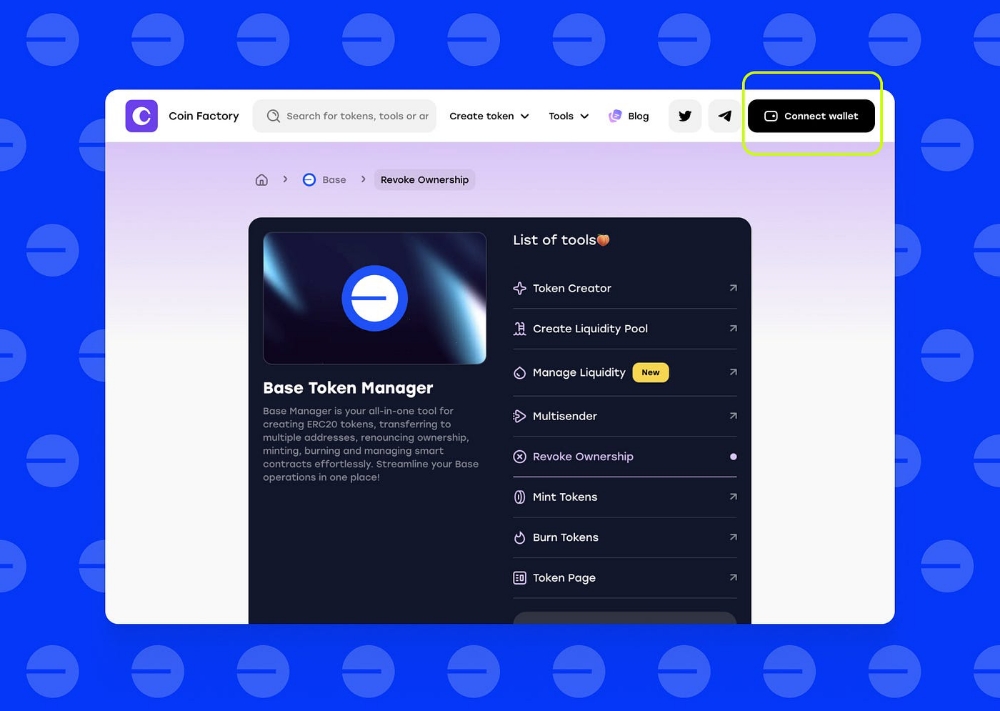
Centralized Architecture: In 2021 alone, up to $1.3 billion in user funding was deployed from his DeFi protocol. The most common factor in these hacks is the over-centralization of the blockchain architecture. Token-issuing exploits and lag-pull schemes, exacerbated by centralization, are two common attack vectors in DeFi breaches. These are often due to the risk of single points of failure within the protocol. Users with privileged access are especially vulnerable to exploits.
External interfaces: DeFi bridges and Web3 oracles represent his two other critical vulnerabilities in blockchain. A bridge is a protocol that allows users to move assets from one blockchain to another. For example, you can go from Polygon to Arbitrum. Because they rely on smart contracts, they are exposed to the same vulnerabilities as other dApps and smart contracts. Oracle is a third-party data provider that provides off-chain data for smart contracts. They are not part of the blockchain network and therefore are not subject to the same oversight and security checks as the rest of the system.
Code reuse: Code reuse is much more common in Ethereum smart contracts than in non-blockchain apps. In the burgeoning blockchain industry, new projects mostly rely on existing development-level protocols. Because the blockchain project is open source, anyone in the industry can access the project's source code and implement it with few changes. This often results in the duplication of erroneous or buggy code, which can compromise network security. Note that blockchain is immutable. This means that interacting with deployed buggy smart contracts always poses a significant security risk.
Misconfigured: This is different from code reuse. Misconfiguration is a serious problem because blockchains act as client-side software in decentralized peer-to-peer networks. Implementing insecure default software configurations can create the potential for serious security breaches.
How to Ethically Hack a Blockchain
Securing the blockchain is the obvious way to protect your investment, your hard work, and your reputation. As the blockchain industry continues to grow and evolve, so do its threats and vulnerabilities. Penetration testing and smart contract auditing have therefore become essential tools for ensuring the security of blockchain-based systems. Penetration testing is a form of ethical hacking that projects can use to identify weaknesses and weaknesses in their systems. Penetration testing helps organizations understand their security posture and identify areas for improvement by simulating real-world attacks.
Smart contract auditing is another important tool for ensuring network security. By examining the code of the smart contract, organizations can comprehensively understand the risks and vulnerabilities within their blockchain-based systems. Taking vital steps to address these risks and exposures can help ensure their systems’ security and the data they contain.
Rob Behnke, 'The role of ethical hacking in blockchain Security' (online,2022) <https://halborn.com/the-role-of-ethical-hacking-in-blockchain-security/#/>.